Hey.
Why is this article needed and why now? You will find the answer in the preface, as well as in the description of what is happening with our neighbors.
Background, or state blocking of the Internet
For three days, the Internet was disconnected in Belarus, and this affected both mobile operators and wired ones. The country of almost 10 million people was instantly thrown back into the past when communications were not available. Such a network outage means losses for many companies, the inability to pay for goods in stores using bank cards, order a taxi from the application, and much more. The lack of the Internet disrupts the usual order of things and makes everyday life worse in all aspects. Also, the lack of a network means that you cannot communicate with other people, as well as work, you cannot even send your mail, respond promptly to anything. For media resources that are directly dependent on advertising, these are wasted days and income that cannot be replenished in any way.
In Belarus, the state has turned off the network for most of the country’s residents. The official version, however, claims that some cybercriminals attacked the Belarusian networks, which caused the shutdowns. This version does not stand up to criticism, since initially the Internet in Belarus was built so that the state could control it as much as possible and could turn the switch at any time, which happened during the presidential elections in the country.
The method of disconnecting the Internet is schematically as follows. Each country has channels that go out to the outside world. In Belarus, the traffic exchange point was initially controlled by Beltelecom; this is an operator completely transparent to the state. Then came the National Traffic Exchange Center (NTSOT), which acts as a special service to control the Internet. It was NTSOT that purchased hardware and software systems for analyzing transmitted packets, that is, intercepting traffic and determining its types. Using DPI, you can regulate access to certain services.
In Belarus, a traffic exchange point is becoming a bottleneck for the Internet. All external channels are not only controlled by the state, but they are also initially limited in terms of their bandwidth. This is a deliberate action to be able to control traffic, plus no independent players are allowed to create such traffic exchange points. Ahead of your questions, I will say that in Russia the approach to building a network is fundamentally different, it is the maximum number of traffic exchange points, many channels, and the Belarusian scenario in our country is extremely unlikely. Also, there was not a single example of the disconnection of the Internet by the state due to certain actions. During the mass rallies, the Internet was not working because of the loads, but not the desire to turn it off on the part of the authorities. We see fundamentally different approaches of states.
Since the life of not only the economy, but also the state as such depends on the Internet today, the shutdown in Belarus was not total. The network continued to work for a limited number of clients – law enforcement agencies, government officials, important businesses. NTSOT disconnected everyone else from the network, and this was done for everyone using the IPv6 protocol, and control of the transmitted information was also in progress. As a result, the use of VPN clients that were not added to the block list allowed us to bypass the established restrictions.
Formally, we can say that there was no physical disconnection of the network, just the Internet for the majority was severely restricted in rights. And therefore, the technical means made it possible to bypass these restrictions, to break through.
See how YouTube traffic fell across Belarus. It did not drop to zero, that is, there were those who made their way to the service, but there were significantly fewer of them than usual.
The situation was approximately the same for all other services, there were no exceptions as such. And here it is important to understand one rule that invariably applies everywhere and always.
With deliberate blocking of the Internet, network connectivity suffers first of all, it is almost impossible to transfer large amounts of data. As a result, for users under blockages, networks and their capabilities are degraded. For example, it will be difficult to transfer a video in high definition, the download will constantly break. Those who block the Internet often use packet analysis and terminate sessions in which a significant amount of data is transmitted, it is set arbitrarily. But messages in instant messengers, mail and similar communications cannot be blocked. Too little data is being transferred.
Only a total disconnection of the network can lead to the fact that it will not work, but this is an extreme measure that almost no one ever goes to. Everyone needs the Internet, so expect it to work one way or another. The question is how to get out and bypass the blockages.
Personal security, searching your smartphone and how to avoid problems
Unfortunately, we always worry about our own safety only at a time when it’s too late to think about it. After all, in order to ensure safety for yourself, you need to take simple actions, it takes a little time, a minimum of effort. But this, of course, is a certain tension and other user habits that deprive us of the usual comfort. Here everyone should soberly assess their risks and what this or that situation may threaten him with.
Several people from Minsk reported that their acquaintances, young people, were stopped on the streets and checked their smartphones, forced to show Telegram and what groups the person was subscribed to. Privacy of private correspondence is guaranteed by the law of any country, and such requirements are illegal. But you also need to realize that when people in uniform with truncheons hang over you, you will not quote laws, the likelihood of a head bang is maximum. And then all that remains is to pray that they do not find something that attracts their attention.
When discussing security issues, I often hear the argument that you do not need to unlock your smartphone, otherwise no one will be able to enter it. The daredevils who think this way have never faced aggression in the real world, when people under threat of beating not only say their passwords, but show themselves everything that they have on the phone. You don’t need to consider yourself a hero, that’s unnecessary. As well as the fact that heroic behavior can lead to health problems.
If you take care of your safety in advance, then with a high degree of probability no one will find anything with a cursory examination of your smartphone. Unfortunately, the least secure device today is the iPhone, and we are not even talking about the possibilities of jailbreaking it, but rather about the fact that by unlocking the device, you will give everything that is in it into the wrong hands.
On Android, there are several tricks that can help you avoid the attention of those who are quickly trying to find some reason to hurt you. Most Android smartphones support the creation of second copies of applications, you can bring the same Telegram to the second number, where it is worth collecting all the channels that you read and think that they can cause a reaction during inspection. The second Telegram icon is hidden somewhere in the folders, turn off notifications in the blind. This is not the best way to hide information, but it will be enough to avoid problems with a cursory search. In this case, you will not pass a thorough check.
Samsung smartphones have a “Protected Folder”, the KNOX system is used here. All contents of this folder are encrypted, this is additional encryption. To get into the folder, you need to enter a password (you can use biometrics, but you need to disable it! Your finger can be applied without your will). The plus is that the folder can be hidden, it simply won’t be on the menu. Disable notifications from the protected folder, and no one will see that you have it in principle. Other interesting points – an attempt to enter the folder will lead to the fact that the content will be blocked after several attempts to guess the password.
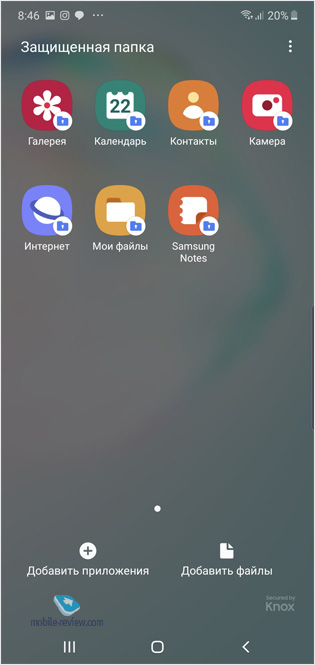
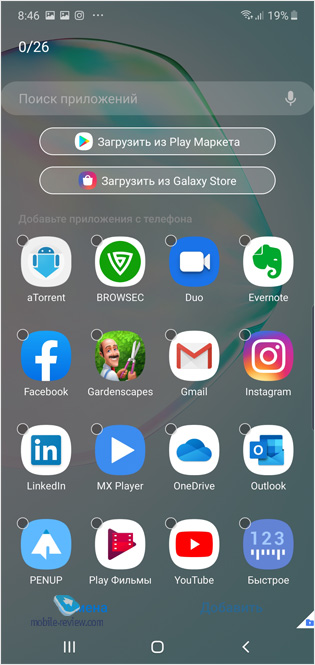

In my opinion, today it is the “Protected Folder” that is the only option to somehow avoid questions during a search. Unlike the option above, when using KNOX, you will be able to withstand picky scrutiny of your phone.
But all this needs to be configured initially, you need to make sure that information security is not perceived as a whim by you. This is what is needed in critical situations, such as the one in Minsk.
I will allow myself a lyrical digression. I do not believe that people cannot read opposition blogs or channels, their right to choose sources of information without censorship, if they are not prohibited by law. Illegal searches, phone checks – all this causes shock. The above describes how this can and should be dealt with if you think that the threat of such a situation is high.
Fight against government surveillance, restore Internet access
So, the disconnection of the network is not total, somehow you can break into the outside world, the only question is how to do it. Some software has built-in utilities for bypassing locks, for example, Telegram has shown itself well, since after a couple of years of fighting against locks in Russia, proxy servers have appeared in the settings that allow you to bypass certain restrictions. In Belarus, many Telegram users made their way out, as they got access through a proxy. Interestingly, many proxy servers were blocked quickly enough, but both the Telegram team and their sympathizers raised new proxies. In the war between the state and Telegram, the messenger won again.
But in addition to Telegram, there are many programs and services that are subject to blocking, but you probably need to work or communicate. How to deal with them? The answer is quite simple, these are VPN clients that can be installed on a computer, smartphone or tablet. The beauty of VPN clients is that they encrypt your traffic and allow you to become “invisible” to those who are trying to keep track of what you are doing. This is not a panacea at all, since such traffic can, in theory, be hacked, get access to the data that you transfer (for example, TOR servers, as a rule, contain certain states, keep track of the secrets of those who use them , such a server is an entry point where information is available and can be intercepted). But VPN clients are better than nothing, you can access the network the moment someone turns it off and turns the switch.
You need to take care of installing the VPN client before the thunder breaks out. Perhaps I was lucky, since I constantly travel to China, where access to many foreign services is closed. Therefore, I have several VPN clients, if one does not work, then I use another. There are both paid services (no traffic restrictions, they work better) and free ones. My favorite app is ExpressVPN, there are many locations around the world, different blockages are easily bypassed.
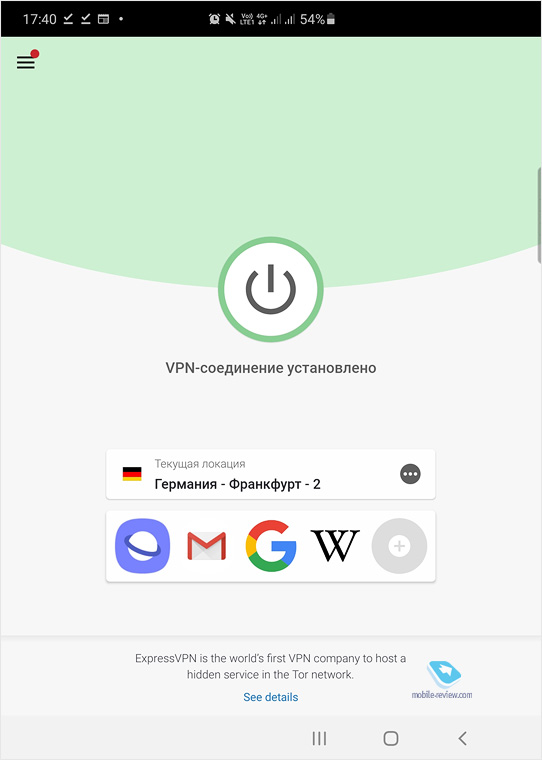
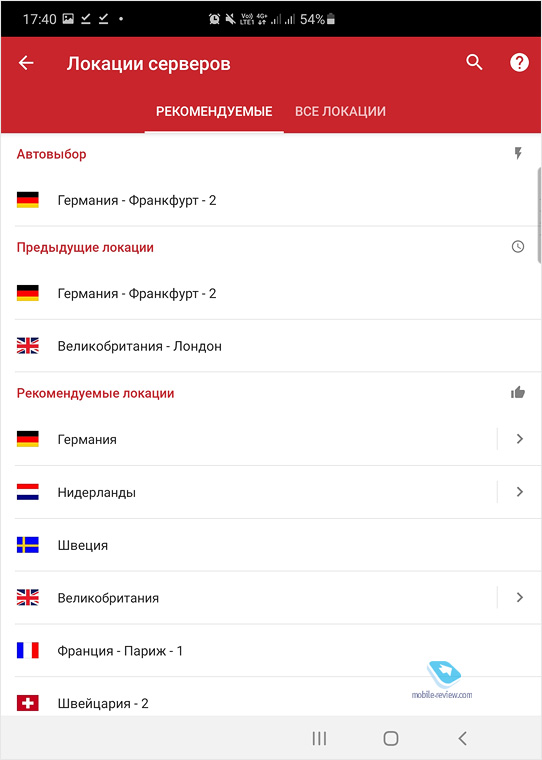
But this application cannot be considered ideal. Also, I am fully aware that they can follow me in it, the only question is who does it. This reasoning is always worth putting into practice. For example, if you live in Minsk, how important is it to you that you can be followed in America? Most will consider this threat to be negligible.
For the paranoid, the use of VPN services that are developed by independent groups can be advised, in theory, they are outside the influence of this or that state. Although, most likely, their independence may turn out to be the same exact screen. But among these services there is not a single one that was developed in Belarus, if you are attached to current events.
When the thunder struck, the number of VPN client users in Belarus was insignificant. Most of the clients were paid or could not cope with blocking, Psiphon showed itself well (its protocol, the presence of different proxies, this application can be safely called a new generation VPN). Look at the number of connections to Psiphon from Belarus since the blocking, the graph speaks for itself.
You can download the application here.
The analogue of Psiphon is Lantern, it is open source software, but it was created in the USA, many servers are also located in this country. How safe it is is unclear. I think it makes sense to pay attention to NewNode, this application promises more security and works well in practice.
As for me, any modern person who is even a little worried about their digital security should use a VPN. The only downside is that your smartphone will discharge noticeably faster, sometimes the power consumption is almost twice as high. Using a VPN gives you additional chances not only to bypass blockages, but also to hide what you are doing on the network. It is almost impossible to do this completely, consider that the network is transparent for attackers and even more so for states. The fact that you and your friends have not yet come to you does not mean absolutely nothing.
What if there is no Internet at all? There is an answer to this too
For those who want to communicate in the absence of the Internet, there is a simple solution – applications that use Bluetooth or Wi-Fi to create a connection, smartphones in such a network act as access points, sending messages from one addressee to another. For the first time such an application was used in Hong Kong, since then many FireChat analogs have appeared.
For example, you can use the Briar app.
Or put Bridgefy on your phone.
But you need to install these applications in advance, before the network outage happened, otherwise you will not be able to communicate with anyone. There are many such applications, you can find the one you need. Please note that you need to choose those applications where there is no registration by SMS, this is the point of your vulnerability, tracking registration from the operator’s side will not be the slightest difficulty.
Short conclusions and wishes
Only one person is responsible for your life and health, that is you. Digital security is considered by many to be something to be neglected. But as you can see from the example of Belarus, this is something that should be taken care of in advance. And here the question is not even that you will be deprived of the usual means of communication or services for entertainment. It is possible that the question will be about your health or freedom. Take care of yourself and your loved ones, try to be a modern person and pay attention to ensuring that your information is protected – on a smartphone, computer, on other devices. Gadgets are already an integral part of the life of a modern person, and their safety is a necessity, it’s time to think about it and take minimal measures to protect yourself. Moreover, it is not so difficult and often you need to spend ten minutes setting up everything you need.
Unfortunately, the statistics are relentless, and they show that most people don’t use VPN clients. Many people completely deny the need to protect their data (in the post-Soviet space, the rampant of viruses, botnets and other evil spirits, this is a consequence of carelessness). Do not be a statistician figure that demonstrates carelessness to your own and other people’s data. Below are a couple of links to help you protect your data and devices.
Related Links
Share:
we are in social networks:
Anything to add ?! Write … eldar@mobile-review.com




