Hey.
From time to time we have materials on how to protect your data on smartphones, but each time we consider only a part of the possibilities that modern devices provide. It seems to us that some things do not require a separate description, this is a professional deformation, since life suggests that many simply do not think about it and do not follow the elementary rules of digital security. The impetus for this text was a letter that I received the other day:
Good afternoon, Eldar.
I have been reading your articles since time immemorial, I really trust your opinion.
The other day I had a situation with my father’s Google account. Once, after reading your article, I bought him a Samsung M10, a good solid phone, so far there have been no complaints. I created an account from scratch and backed up my account.
The other day I receive a letter that the password has been successfully recovered and all that. I know that my father is not yet so versed in the phone to change something there, especially to do something with the account, but just in case I contacted him and it turned out that he was not doing anything. I immediately tried to change the password, to which a message was sent to me that an SMS with a password was sent to two phones, Motorola and Samsung. I know for sure that there are no such phones in my family, so I immediately tried to block the account, but due to the fact that I am at sea and my Internet speed is not the best, I managed to do it somewhere in half an hour. Google sent a warning that they will figure it out and give an answer within a few days. A couple of days later, a letter came that everything is in order and I can restore my account and continue to use it, which I did. Everything, it would seem, is ok.
But a day later, the phone automatically synchronized the data with the account and the entire phone book disappeared. Some left numbers appeared. He managed to restore literally 10% of everything he had.
After this incident, I just wondered what if this happens to my account. I am using a Samsung Galaxy S9 +. The first thing I did was move all the phones to the device’s memory, turned off automatic synchronization, I transferred all my notes from Google Kip to Samsung Note. there any note can be protected with a fingerprint.
There are no more ideas yet.
Please write an article on what to do in such cases, how to protect yourself from such hacks, at least using the example of Samsung phones. How does the account algorithm work on these phones? there are two of them, Google and Samsung. Which account is better secured? How do I use the protected folder? This is generally a pain … How many times I have been using the phone, but I cannot understand the logic of this folder. In general, please write everything you know on this issue. I think the readers will be grateful, including me.
Thanks in advance,
Konstantin
The questions asked in the letter are very extensive, but I will try to answer them in this material, or set the direction in which you can study this topic. Since I use Samsung smartphones, and they have the maximum number of different security functions, the story will be based on the example of these devices. Something is unique to them, for example, the KNOX system that protects your data, something is part of the protection from Google. Therefore, the text will be of interest to any owner of an Android smartphone, it describes the standard scheme for protecting their data.
Content
- Digital identity – which threatens any person
- First setup of an Android smartphone – passwords, device search, data protection, clouds
- Spoof letters
- Password / biometrics protection
- Find Lost Phone / Remote Lock
- Memory card and encryption of information on it
- Cloud services for storing your data
- How to use your smartphone safely – what is important to know
- As an afterword on safety
Digital identity – which threatens any person
We live in a world where any information is sold. Social networks sell patterns of your behavior to advertising companies or banks, the latter trying to use this information in different ways, including selling it further. The sale of digital personalities is popular on the black market; these are accounts of people with which you can pretend to be another person on the network, put on his image. The cost of such an account varies greatly, from one dollar when buying hundreds of “personalities” to several tens of dollars when choosing a suitable account, which is needed for certain purposes. Criminals pretend to be other people for a reason, for them it is an opportunity to imitate a living person, hide behind them as a shield and confuse law enforcement agencies. Unfortunately, most people treat this threat as imaginary, completely careless in how they monitor their own safety and brush off the basic rules of digital hygiene.
Supporters of the openness of their own data often talk about the absence of personal enemies, about the fact that they have nothing to hide. They are offended when you ask the question, “Do you close your apartment or you don’t have locks on the doors?” They say that this is completely different and you cannot compare the security of your home and “some kind of telephone”.
People don’t fully realize that a phone can tell more about its owner today than even the closest surveillance in the past. Here you can find all your movements, conversations and correspondence, access your photos and videos, and a notebook. See what Google knows about me and my movements. Moreover, you can watch both specific days with very detailed routes, and just cities and countries.
You can also see in your account everything that you searched for, read and even what applications you launched on your smartphone. All this is available to the owner of an Android smartphone in a personal account.
Is it striking? But this is only part of the information that you see, and when your account is hacked, it will be available to attackers. You can use this information for any purpose, blackmail is not at all the most obvious, although it is often present in the list of cybercriminals’ favorite tools. Most victims do not discuss these kinds of problems, as they paint them in the wrong light and it is difficult to estimate the number of such stories.
But for sure you have come across messages that your friend / comrade needs money. Usually they ask for not the largest amounts, but this is an urgent matter and they need to be sent as quickly as possible. Such a message can come from mail, in Skype (it is full of holes and it is broken constantly and non-stop), in another messenger.
If an attacker gains access to your correspondence, for example, mail, then he can simulate such an attack much more thoroughly and achieve success. They will ask for money on your behalf and this is an unpleasant moment. No one is immune from this, but it is very difficult, if not impossible, to hack those people who adhere to the minimum rules of digital hygiene. And here we come to the first rules that will help to avoid problems in the future.
First setup of an Android smartphone – passwords, device search, data protection, clouds
It will not be superfluous to repeat the banal safety tips, as many people know them, but they do not always follow them. The password for a Google account must be unique, it must not be standard and similar to the passwords that you use in other programs and applications. It’s simple, but many people forget about it or consider it unimportant. But this is extremely important!
Spoof letters
The next important point – do not open links to Google services from letters where you are asked to log in, often these are fraudulent letters, your password is deceived. Spoof sites look exactly the same as the native services of the company. It seems that everyone knows about this, but the method of deceiving passwords has not lost its relevance, scammers use it all the time.
Password / biometrics protection
Biometric phone access protection is an easy way to protect all your data – you can use facial recognition or a fingerprint sensor. Both methods are quite reliable, the choice is yours. Samsung smartphones have two settings for face recognition – fast and normal. In comparison with Chinese smartphones, face recognition works exactly the same, it is fast recognition. With normal recognition, the speed is slightly slower, but the level of protection increases dramatically.
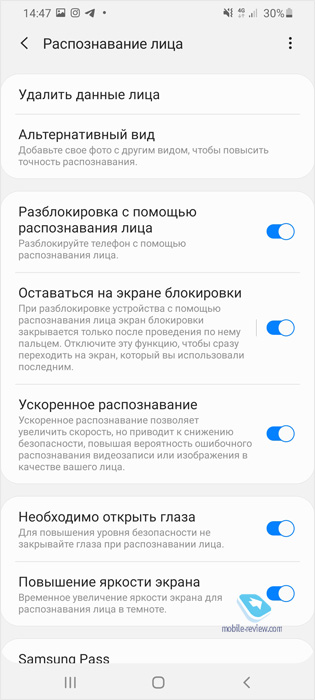
Which option should you choose? It depends on the other settings you are using. For example, I have accelerated face recognition, since all important information is “hidden” in a protected folder and it is impossible to access it without entering an additional password or fingerprint. However, it is also impossible to hack a quick unlock today, neither a photo nor a video allows you to do this. On a couple of models, this protection was disabled in the past, but the bug was quickly found and fixed, it lasted for about a week.
You can use not only biometrics, but also a digital code or pattern, these are simple ways to protect your data from anyone, no one will gain access to your data without your knowledge. Leaving your phone without a minimum level of protection is not worth it, it’s important. Nobody thinks that a smartphone can be stolen or you will lose it. Without minimal access protection, you yourself will give all your data to other people.
Find Lost Phone / Remote Lock
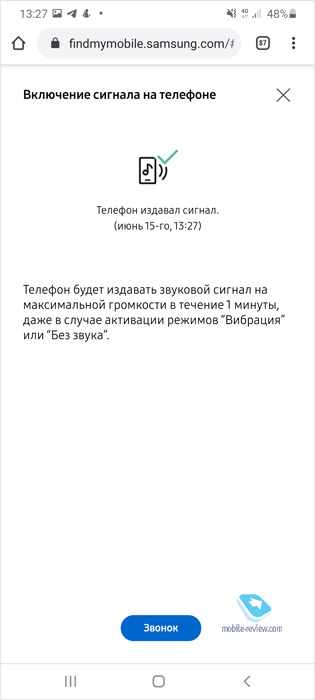
Google has a search for a lost phone, on the map you can see where the service “saw” your device last time. The accuracy of determining the coordinates is sufficient to understand where to look for it. You can also make your phone beep even if it is in silent mode. And this is very convenient for finding a smartphone at home when you do not understand where you put it.
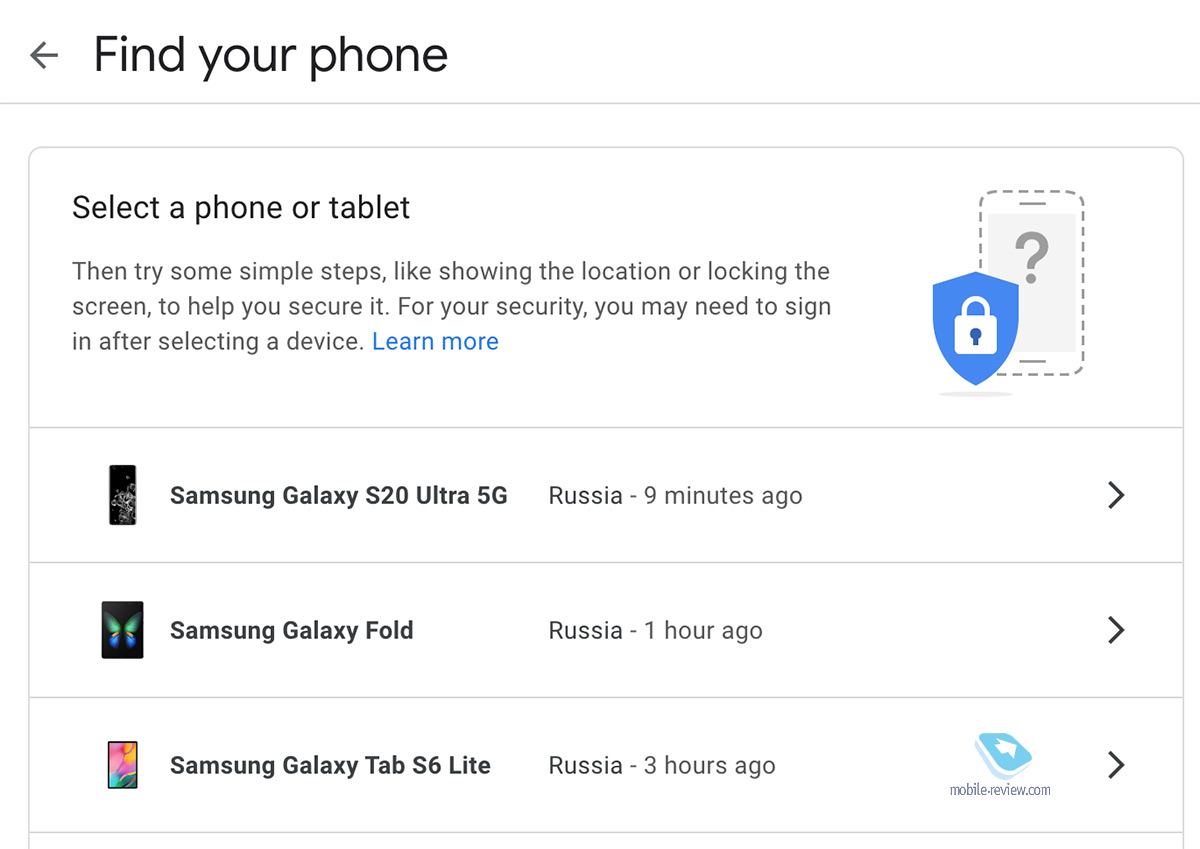
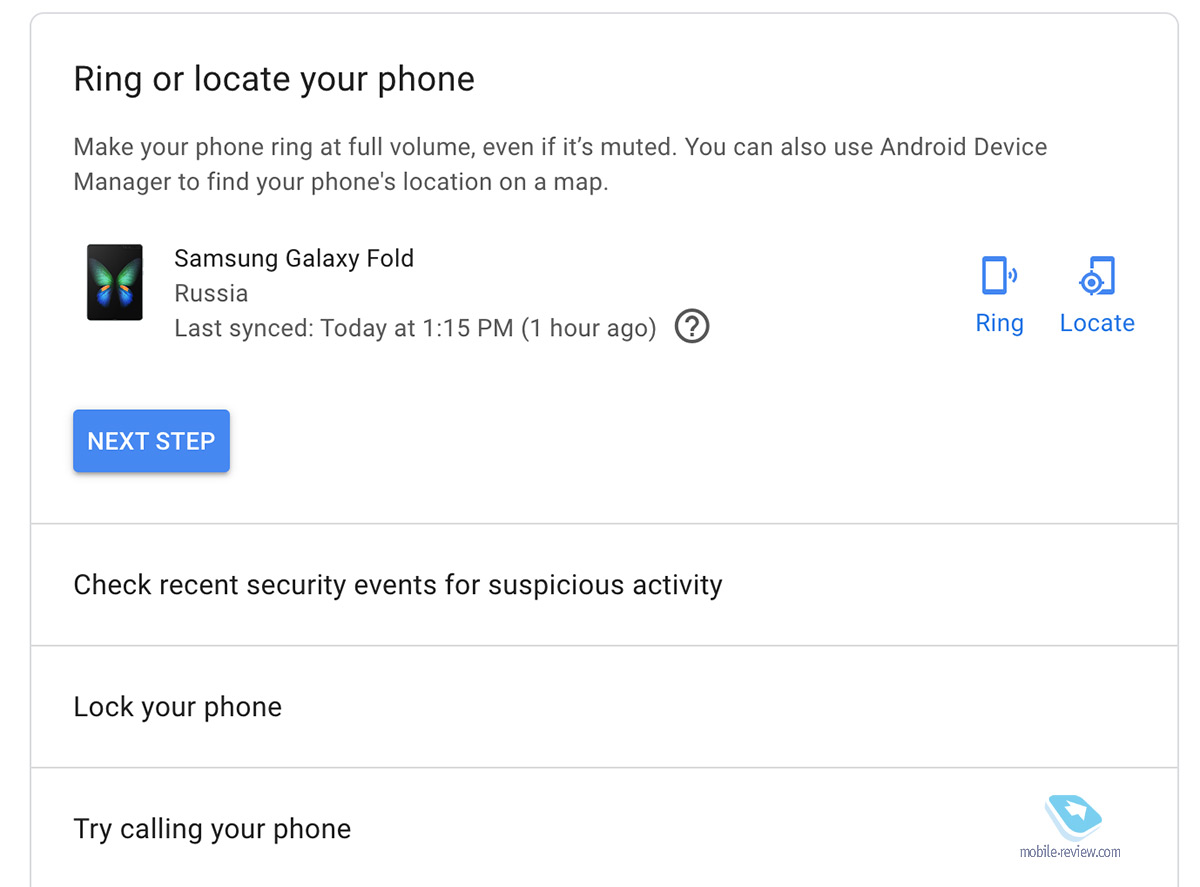
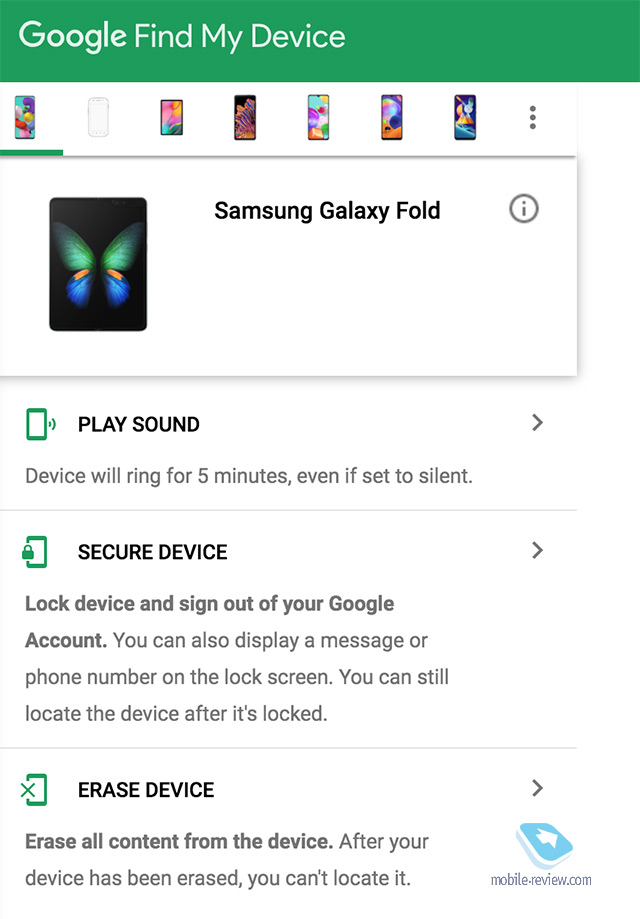
Samsung Account has a similar service – Find My Mobile, it seems to many that it is redundant and duplicates the service from Google, but this is not the case. You can see all your devices, you can track them (these are both coordinates and connected WiFi networks), as well as block them remotely (and unblock them as well), delete data (make a backup before deleting or blocking, also remotely), get a list calls / messages from the device (this is a unique feature that will be of interest to many).
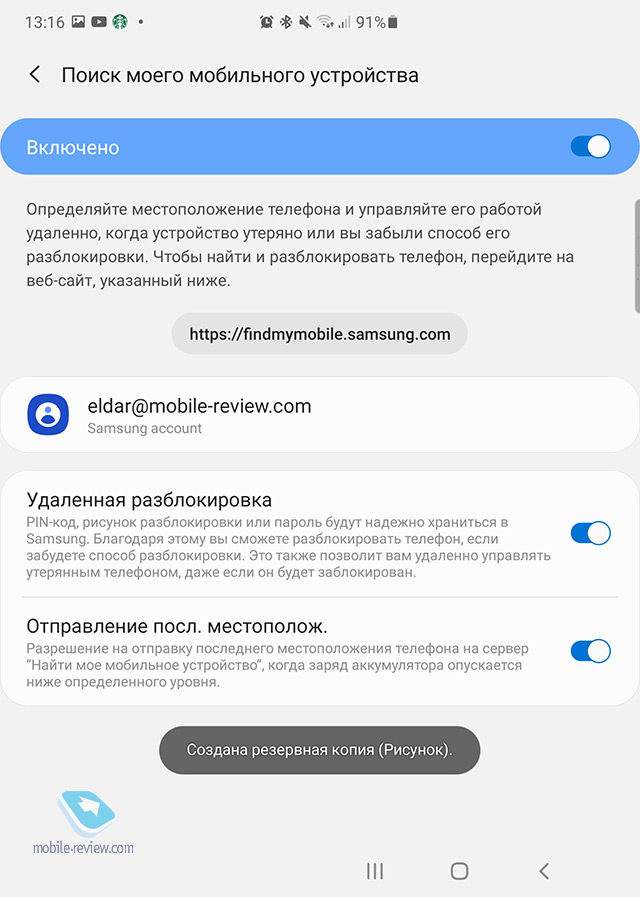
As a curious thing, you can assign “trustees”, that is, give remote access to find the phone, its location, enable emergency mode to other people.
We must not forget to give permission on each phone to send coordinates to this service.
As you can see, in the case of Samsung’s service, you get additional features that can help you save information even if your phone is lost (but it will be online and will not be turned off). If the phone is stolen and someone tries to use it, the built-in data protection will prevent intruders from reading anything. But if for some reason they know your password, then you can delete all data remotely.
The broadest possibilities, but access to them opens only in one case, if you spent a few extra minutes during the initial setup of your smartphone. Does it matter? Certainly. Let me emphasize that these features are standard for any Samsung smartphone.

A little-known fact in wide circles, when you reset the memory of a Galaxy smartphone, if it had a Samsung account, then you need to log out of it (that is, you need a password!). A forced hard reset will not lead to the fact that the one who found / stole the phone will be able to enter it, he will have to enter the pattern or password. This is an additional layer of protection, and once most people use these tools, phone thefts will disappear by themselves, they just won’t make any sense.
Memory card and encryption of information on it
Android smartphones use memory cards; by default, all information on them, unlike the internal memory, is not encrypted. Therefore, when you lose your phone, the memory card becomes a point of vulnerability, all information on it is publicly available, as a rule, videos and photos are stored there. To prevent this from happening, you can encrypt the memory card and it will only be read in your smartphone.
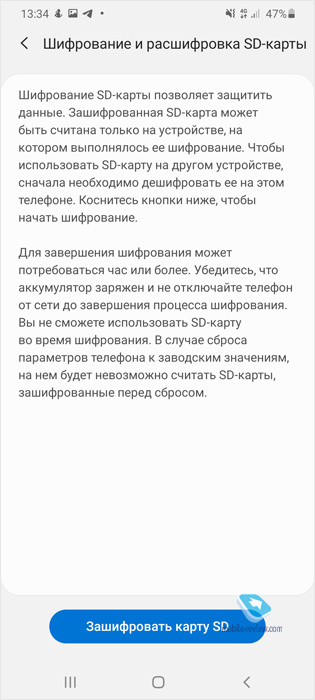
The downside is that you can decrypt such a memory card only in the same smartphone. And if for some reason he “dies”, then the memory card will become useless, you will not be able to extract any information from it. On the other hand, it will be correct to configure cloud services to store all important information, so that it is synchronized every day and then the loss of a memory card or the entire phone will not affect you in any way.
Cloud services for storing your data
Most people are incorrigible optimists and almost never think about something bad, believe that nothing will happen to their devices. Most of life this happens, but sometimes something goes wrong and then it becomes bitter that you have not configured the cloud services so that your data is stored in them.
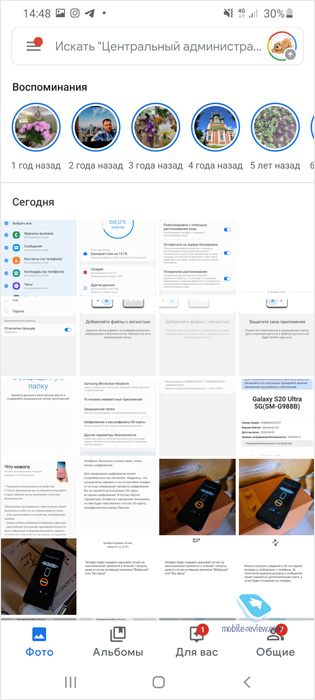
For example, it makes sense to enable unlimited storage of all your photos in Google Photos, it does not cost a dime, but you will always have an archive at hand (unlimited is available only when you select “High quality” photos, and not the original size of the images, but that’s enough. is not it?). And also you will get a search throughout the archive, when you can search by people’s faces by typing the name of an item and so on. Conveniently.
In principle, you can use any other third-party services, the same Yandex.Disk, if for some reason Google Photos does not suit you.
Samsung smartphones have Samsung Cloud, where it is worth saving all the settings of your smartphone – the desktop, the arrangement of icons, keyboard settings and much more, for example, notes. This is a very convenient way to sync data between an old and a new device, or between two models if you have two smartphones.
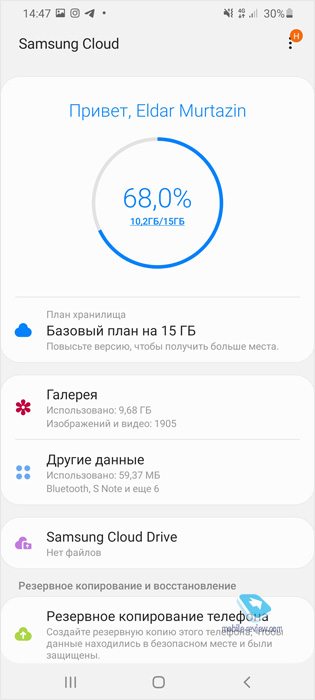
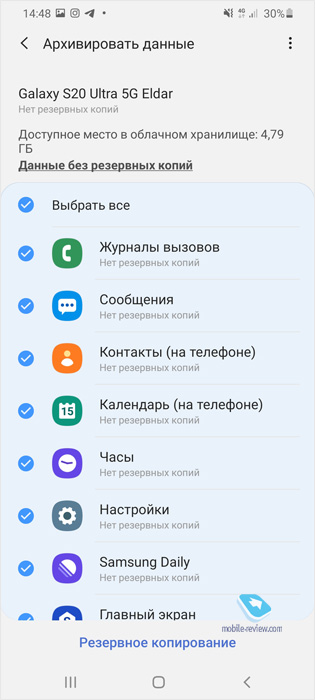
A copy of your photos and videos in the cloud, your phone settings is the confidence that you won’t lose anything. These services do not require special attention, you configure how you want to synchronize data (WiFi or cellular network) and just forget about it.
How to use your smartphone safely – what is important to know
Any smartphone is a complex system, over time, Android can find certain vulnerabilities that can, in theory, be used to attack your device. The likelihood of such an attack is extremely low for most people, but both Google and device manufacturers release security patches, they come out monthly.
For example, Samsung is enabled by default to automatically receive software updates, including security patches. Every month, you receive such patches, the installation process takes at most a few minutes (there are large updates, but they are released less often, then a little longer).
Surprisingly, many people refuse security updates and do not install them. Why? It seems to them that this somehow negatively affects the smartphone, which is of course a delusion. Any bug fixing is good and therefore it is necessary to install such updates. At Samsung, they are released monthly, which gives the maximum level of protection against the problems inherent in the system itself from the beginning.
As a rule, users are the weakest link, they install programs on their smartphones on their own, which begin to monitor them or steal data, and allow them to be hacked. The first thing to remember is that you can and should install programs from the Google app store, where apps are checked for viruses and hidden features. This does not guarantee 100% that there are no such hidden features in applications, but it reduces this probability to a minimum.
When installing an application, you are asked what rights to give it, to which sections of the phone it can have access.
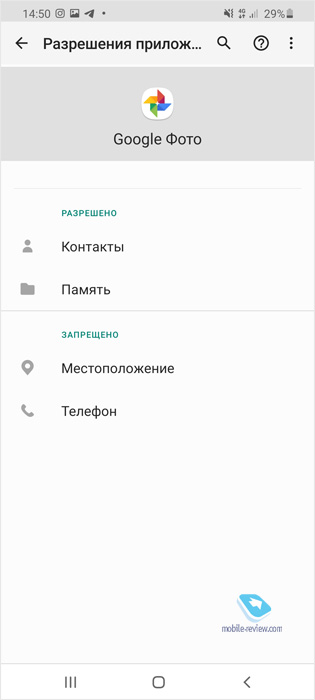
If you trust the developer, you know that this is a large company, then allow whatever it requires. Otherwise, open access only to those permissions that seem logical to you. For example, the Flashlight app hardly needs access to your photos or notebook.
In the Samsung app store, there is an additional check of applications for hidden features, you can install programs from there. But what you don’t need to do is install APK files (programs for Android) that you found in unknown places on the network. For example, it can be a jailbroken toy sold for one hundred rubles in an official store. Some people are tempted to get such a game for free, but by installing the application, you are also most likely installing a Trojan program that can spy on you and steal all your information. Avoid installing apps from third-party sources, or do it wisely when you understand exactly who created the app, what it is for and what risks it carries.
There is another point that few people realize and understand, this is the ability to create a smartphone in a smartphone, hide some information and applications so that no one will even guess about them. This is a unique feature of Samsung smartphones, which appeared thanks to the KNOX security system, which not only encrypts data, but is also able to safely hide it.
In the settings of your smartphone, you need to enable “Protected folder”, it actually creates a duplicate of your smartphone and its settings. Inside this “folder”, you can install second copies of applications, select other accounts to use in them, for example, create a second Whatsapp or another messenger. Or you can copy applications from main memory.
For the protected folder, you can even set up another Google account, that is, you really get two smartphones in one. And the cherry on top is the fact that you can hide the “Protected Folder” icon from the menu, no one will guess that you have extra space with other applications and data. You can copy photos, videos and other files to the protected folder, as well as remove them from this area.
The idea of a “protected folder” is simple and straightforward, it, like a nesting doll, contains another phone in which you can configure everything that is of great importance to you and you think that it may be of increased interest to someone. Even if attackers gain access to your main memory, somehow they will be able to pass the built-in protection (which is almost impossible, rather you will unlock the device yourself), then they will definitely not be able to find and open the protected folder without your participation. To date, these capabilities simply do not exist, they are unique.
As an afterword on safety
Digital safety and hygiene are essential to avoid a host of potential problems and annoyances. But the most important thing is that if earlier you had to spend time and money to protect yourself and your information, today all protection methods are built into Android, they are simple and understandable. All the settings take a little time, you just need to figure it out once and then follow the path that you have chosen.
Use biometrics correctly to prevent unauthorized people from accessing your smartphone. If you want convenience, use automatic unlocking when you are at home when your smartphone is on a certain WiFi network, or Bixby scripts for the same purpose. Our smartphones can do so much that most people don’t even know about these skills, but in vain.
The protection of personal data is important and there is no need to imagine that you are of no interest. Any data is of interest to intruders and they can use it in one way or another. Digital security should be as commonplace as brushing our teeth to stay healthy. This is digital hygiene and a modern person must follow it.
Hope this post has taught you ways to protect yourself and your device. It takes more time to read this article than to set up your smartphone and its defense lines. If you are not in the mood for certain things, then do not be lazy and do it now, do not put it on the back burner. And for those who are setting up a new Android smartphone, this material will be useful. If you are very worried about the protection of your data, you focus on this moment, then choose smartphones where the level of such protection is maximum.
Back to content >>>
Share:
we are in social networks:
Anything to add ?! Write … eldar@mobile-review.com





