Hey.
Russian people believe in myths more readily than in everyday reality. Believes earnestly and to the point of blue in the face, although this belief under itself has no basis, but they, in fact, are not needed. Perhaps this is part of national self-identification, when everyone is lying around, which means that the truth looks very different from what we are told. When thinking is built from the opposite, and attempts to understand how everything is arranged and works are not made. With great interest, I watch in real time how a persistent myth arises that in Russia it is possible to access the data of subscribers of cellular operators, order a printout of calls, SMS, other information from billing, including geolocation and movement of people! When ordinary people think that this is possible, they can be forgiven for not knowing the specifics of the issue. But when people who consider themselves telecom docs begin to carry heresy, then there is a feeling of the absurdity of what is happening. I don’t know whether for political reasons they sacrifice reality for the sake of the conjuncture or there are some other reasons, but fairy tales are created before our eyes.
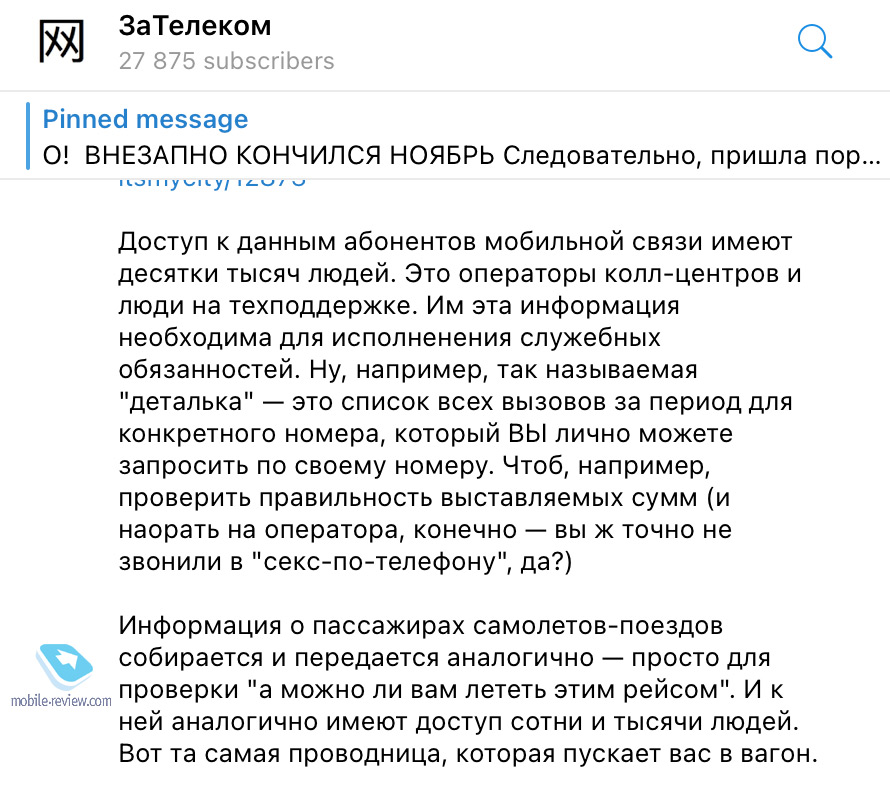
I will quote the popular Telegram channel about telecom (in fact, rather about how bad it is to live in Russia under a bloody regime, but this is particular): “Tens of thousands of people have access to the data of mobile subscribers. These are call center operators and tech support people. They need this information to perform their official duties. Well, for example, the so-called “detail” is a list of all calls for a period for a specific number, which YOU can personally request by your number. To, for example, check the correctness of the billed amounts (and yell at the operator, of course – you certainly didn’t call the sex-on-phone, did you?) ”.
I don’t know how the system works in relation to passengers of trains and planes, but I can tell you how it works for telecom operators, in particular, in the big four – Beeline, MegaFon, MTS and Tele2. I’m only afraid that my story will not leave a stone unturned from the statement above, since this is a lie, rude and outright.
When they lie to us, they constantly try to show themselves off, for example, overestimate the numbers. Have you ever wondered how many people work for each of the operators? I’m sure not. Let’s take a look at the MegaFon website, where these figures are given and are not hidden anywhere. The company employs 40 thousand people, they are employees of all divisions, retail “MegaFon” and so on. Literally everyone, without exception, including top managers and cleaning ladies in the office. If we imagine that all four operators have a similar staff, then four of them will get a little more than 150 thousand people. And the statement that tens of thousands of people have access to subscriber data is, to put it mildly, incorrect.
How does the work within the operator work with personal data, including how billing works, which contains all the information about your calls, expenses, sent and received messages? What exactly does the operator store? You need to deal with this in order to understand what data and where can flow.
Operator billing stores the following information for each personal account:
- calls (duration, number to which or from which they called, time);
- SMS (from whom or to whom, SMS size, time);
- Internet sessions (session size in KB, time).
I want to emphasize that a personal account is tied to a specific person (as an option, an organization, if it is a legal entity), but employees with a certain level of access can see it. The operator does not record calls or SMS for subsequent listening or reading, can only see the very fact of this or that communication, the number with which the communication was. For Internet traffic, the operator easily and simply cannot see where you went, what you looked at on the network and what the GB package was spent on. This is especially painful in roaming when you are trying to find out where your data has leaked and who is to blame (by default, no one believes that his device is doing something on its own, and the operator refuses to explain the consumed traffic and simply cannot).
An important clause about the special services and the law on investigative and operational measures, which has been in effect in Russia for the last couple of decades. Operators put black boxes on the network, they duplicate all traffic, which allows special services to gain access to any information and potentially store it or intercept it in the moment. Similar systems work in most countries of the world that have the ability to install them – the USA, Germany, Israel and others, there is nothing specific for Russia. This is not a means of tracking individual people, but rather a massive tool that allows you to catch this or that information in the stream. And the adoption of amendments to the law on communications named after Yarovaya is just an attempt to add another tool that will be aimed at specific people. It is one thing when the whole stream goes in a crowd, it is quite another when you have information with calls, SMS and traffic for specific people and it is stored for some time. A sort of time machine when you can pick up information on specific numbers after a while. There is little sense from such a system, it is rather useless than useful for the special services, the latter resisted these amendments as best they could. The reason is trivial, these are additional complications and obligations that are imposed on them.
The non-selectivity of the systems described leads to the fact that in relation to the persons being developed by the special services, targeted tools are used, all their means of communication are under control. These are already other tools. Neither the police nor the Ministry of Internal Affairs as a whole can get access to one or another operator information about subscribers without a court decision, such a tool does not exist. A paper trail in the work of law enforcement agencies with operators is always present, it is impossible to get a subscriber’s printouts on a call or otherwise. In the mid-90s, the system did not work that way, but after a series of scandals, everything changed and it became that way.
Personal data of subscribers is the information that is considered especially important within each operator. And this data is guarded, the whole system is built so that no one can get access to them, even when they get to work inside a telecom operator.
A very limited circle of people has full access to billing for specific subscribers, each operator has dozens of people – security service, sometimes financiers, less often technical specialists. The databases are specially separated; all information about a person and what he does on the network is not stored in one place. For example, billing knows everything about your calls, but it is impossible to look in this geotag database where the phone was at the time of the calls. This is a separate technical base, which stores information for all devices, and you need to isolate a specific device using separate requests. This is not a matter of a couple of mouse clicks when a map appears in front of you and on it the subscriber moves with his device. Operators have never had the task of tracking the movements of subscribers and visualizing them, storing them in a convenient form, hence the difficulty with such information.
Information about subscribers is not only divided into different databases, but also access to them is regulated, each call is recorded. For example, an ordinary technical support employee cannot log in on his own and see all the data on your phone number. This requires several events occurring simultaneously:
- he is on a work shift;
- a call came in and you provided your details, including your password.
Only after that, he sees your data, and even then not in full. Knowing the information that you provide to technical support, you can already look at everything requested on your own.
Let’s imagine for a moment a situation when someone agrees with technical support to look at the data of my phone without my participation. You cannot simply log in without an open ticket (service request). In order for such a request to take place, you need to know a number of information about me. Let’s say that my passport data was found somewhere, the password was picked up, or it is not needed. The only thing left is to get to the employee that you need by calling the general line. These are hundreds of people, it is almost impossible to get on the right one. You are somehow fabulously lucky, you got on an accomplice, and he is ready to save all the details for you.
How will he do it? Helpdesk are open cubes in which employees sit. They cannot save anything from their computers or send to their mail, upload to the cloud. Taking pictures of your computer screen on your phone when your colleagues see everything you do? At the very least, this is strange and will lead to a conversation with the security service.
Regular support staff live under very tight regulations and cannot view anything without leaving digital footprints. Moreover, the security service always looks at the history of events, looking for extremely curious employees who are trying to climb in and see what they are not supposed to.
Employees at a higher level? They are given a greater degree of freedom, but this does not mean that they are outside the control system. Exactly the same way is limited access to the storage of information, the ability to transfer, and so on. I will reveal a terrible secret, usually technical support has access only to the information that the subscriber himself can receive in his personal account, request it as standard in the application or on the website. There is almost never anything beyond that.
Programmers? Maybe these brave guys are a point of vulnerability for operators? But they are under even more supervision than the support team, moreover, they do not need access to the databases and information themselves, the structure is important for them, but not the data. It’s the same story with financiers.
There are no simple, publicly available ways to access subscriber data. This is a myth, but it is very well cultivated, and here is the time to ask the question, who does it and why.
Scammers for Jealous Husbands and Wives – Mass Market Fake Data
On the network, you can come across dozens of advertisements that you will be provided with call details or calls with geo-location for any operator. That is, you will be given information on a specific subscriber, and the service is offered for a small fee.
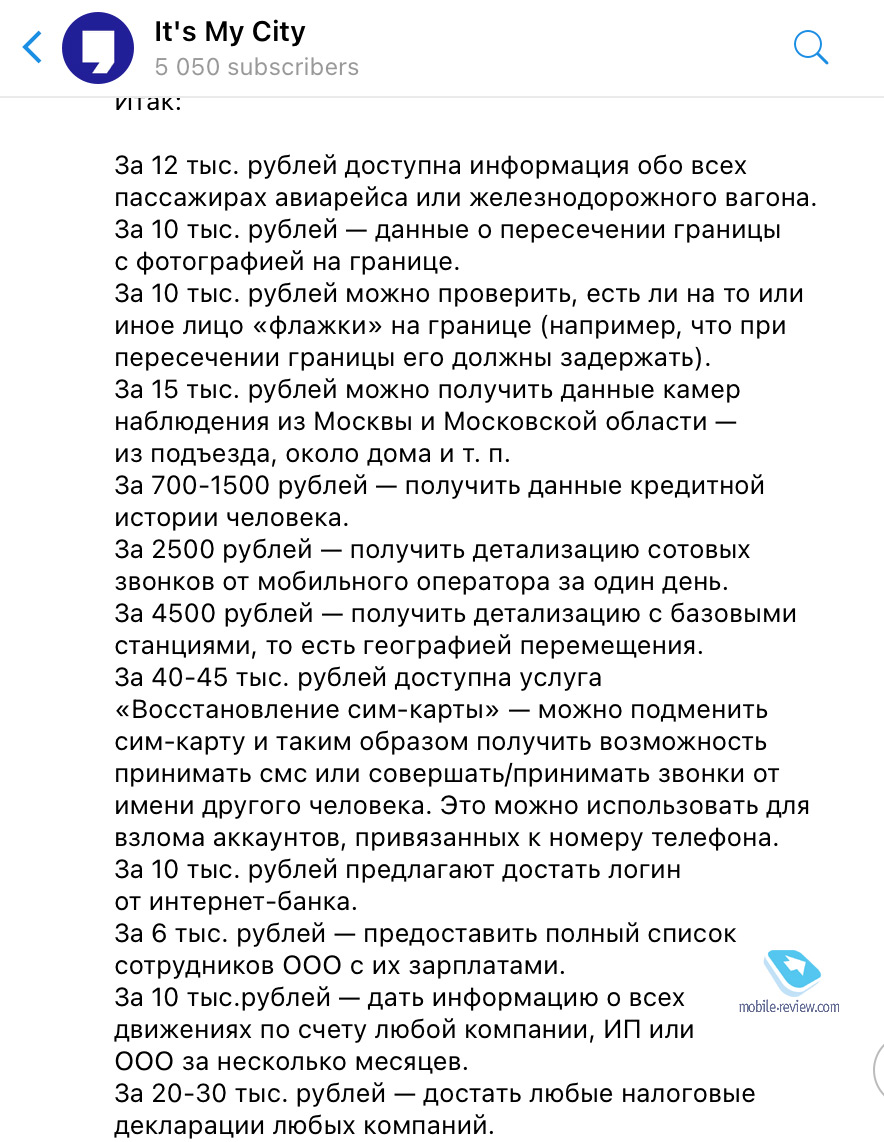
We are only interested in what is connected with operators, I do not know thoroughly about the operation of other systems, so I will not talk. I will quote the rates:
- For 2 rubles – get detailed cellular calls from a mobile operator in one day.
- For 4 rubles – get detailed information with base stations, that is, the geography of movement.
- For 40-45 thousand rubles, the service “SIM card recovery” is available – you can replace the SIM card and thus be able to receive SMS or make / receive calls on behalf of another person. This can be used to hack accounts linked to a phone number.
- For 10 thousand rubles, they offer to get a login from the Internet bank.
I’ll start with the “SIM-card recovery” service, as it is practiced in many operator stores and an unscrupulous seller can really issue a new SIM-card to almost any person. He needs to close his eyes to another passport or a fake power of attorney, and voila, someone else took possession of your phone number for a while. This is quite real, this is where the point of vulnerability lies. It is also an opportunity to order details of calls, SMS and other services painlessly and quickly. There is only one problem: the victim will quickly guess that something is happening, because the operator will send an SMS stating that a new SIM card has been requested. And your phone number will simply be silenced. Therefore, something like this is almost never done to obtain detail.
Let’s put aside the scammers who ask for an advance payment for their services and then disappear, there are about half of them on the market. Almost no one gives you the opportunity to familiarize yourself with what you buy in advance, it is always a pig in a poke.
Every two years I look at what has changed in the “breakout” market, order details and other information using my phone numbers. In this case, I do not violate the law in any way, since I buy information about myself, beloved. But if you try to do something like this, even for your wife, the consequences can be extremely unpleasant.
Quite a noticeable layer of performers is ready to work for a small fee. They ask for a phone number, then try to find information on it in open sources. People have no idea how often they leave their phone number somewhere on the network, in different services. But this is only part of the story, then the most interesting and funny part begins. In my case, I always issue new SIM cards, numbers that I have not used. I call between them, create a kind of semblance of activity for a couple of days.
You unexpectedly receive an SMS with a link to the prize, you are offered to receive some amount of money free of charge, you just need to fill out the form and put the application on your smartphone. A good old trojan is waiting for you if greed overwhelms you (money will really pay you). Usually, the Trojan does not steal information, but leads you to a fake operator login page, where you need to enter your password. Everything is extremely banal and simple.
I don’t buy into these tricks. I’m waiting for the performers to bring me something valuable. As a result, I get a dummy for my money, sometimes it’s just a set of some numbers and calls that have nothing to do with reality. The sellers do not get in touch after that, they add my number to the stop list. They do not need an angry victim, and deceived people, for obvious reasons, do not write on every corner about how they were divorced.
This does not mean at all that it is impossible to get the details of the subscriber’s calls. One way is described above, but there are others, you can find an insider inside the operator. But the price of his services will be completely different, the simplest story starts from 100 thousand rubles, and this is a very small amount of information. People with access to information risk more than just their workplaces, they face criminal prosecution, and for such tricks, several people every year are sent to places not so distant. There is always a temptation, but one cannot say that this is a massive story accessible to everyone.
99% of what is offered on the shadow Internet as a “breakout” of telephone data is branchy cranberries. The hallmark of this cranberry is the ad itself and the low cost, which cannot be so by definition. Detailing is a piece and very expensive product. Speaking about geotags with detail, I can’t help but note that this is a great fantasy of scammers who came up with a product that customers need. In the operator databases, there is simply no such information in an explicit form, and it can be obtained in rather complicated ways. And along the way, light a huge security beacon above your head.
Operator databases – leaks and other tales
There have been no data leaks from operators in the market for a long time, so that all data on subscribers can be found. And then, the previous leaks concerned the names of subscribers and the data of their passports, but not billing as such. There has never been a data breach on the market with detailed details of individual subscribers. Suffice it to say that it is simply incredible for the size of such a potential base.
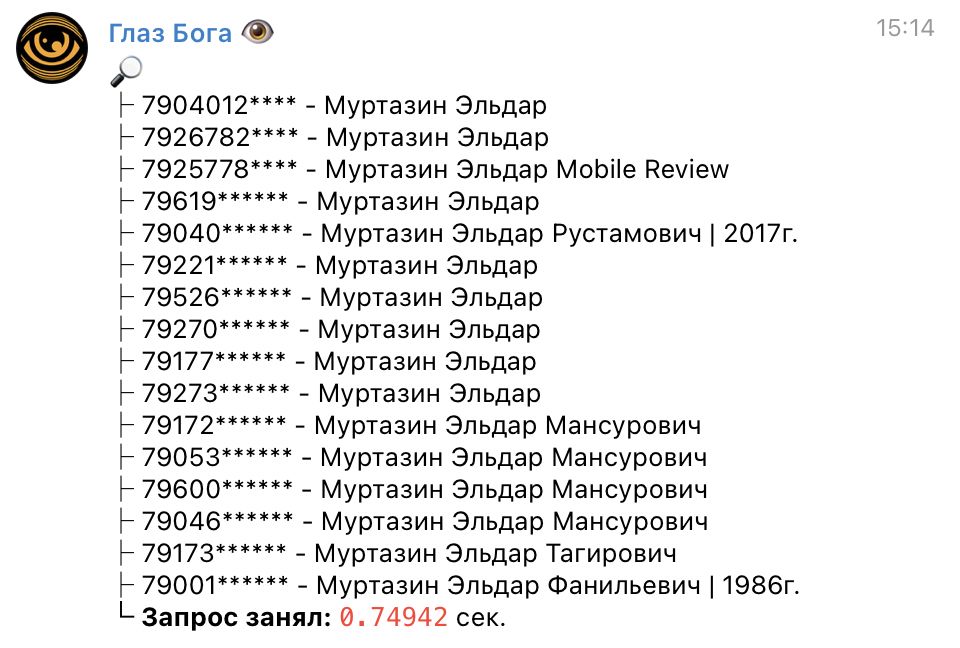
It seems incredible to the layman that he can find his phone somewhere. For example, one of the telegram bots collects information from open sources, you can search there for yourself by last name.
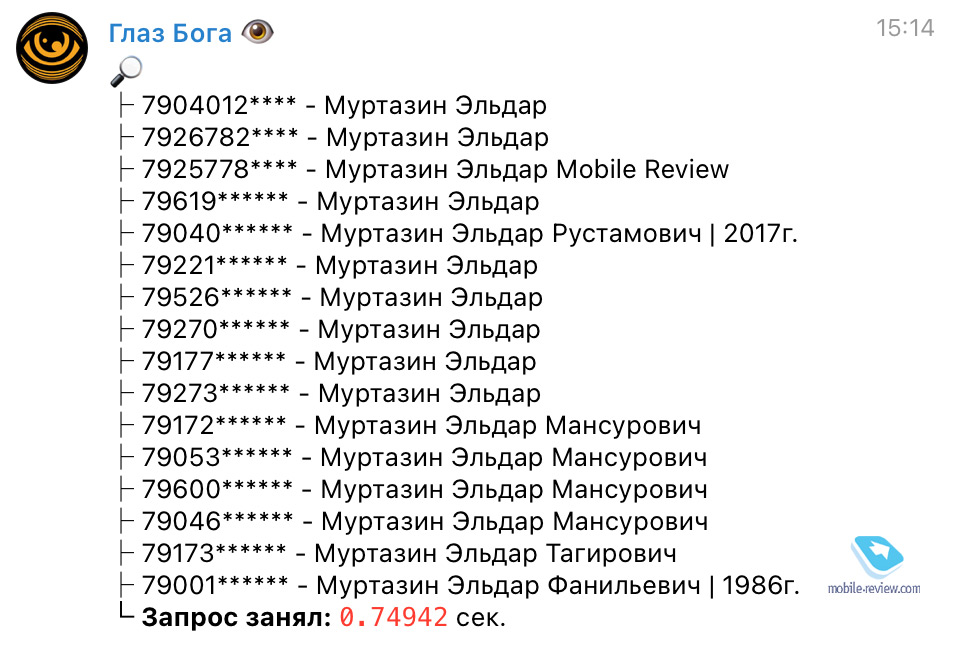
I looked for myself, I found one phone number. Judging by the fact that the site is recorded there, this is someone’s notebook in one of the services “Who called”, when people put the program themselves and give access to the contents of the phone book. Not impressive at all, since you can find a lot more information in open sources, and there is no secret in this. About five years ago, someone posted my tax returns, a person thought it was some kind of special secret. I was surprised by my calm reaction to this.
Operators are not interested in subscriber data leaking somewhere. And the reason here is not just that they are obliged to store this data, but that after each such emergency there is a debriefing at the FSB level. And this does not bring anything good for the operator, according to the results there should always be a person who sold access to the side, and he is punished.
In 2020, more than 20 people were arrested who provided data on operators’ subscribers. Of these, 19 people worked in retail stores and had very little access to the operator’s base, nevertheless, they did business on this. Now they face up to five years in prison. The myth that you can buy real detailing and sell them on every corner is very tenacious. But having tried to do this more than once, I can argue that this is just a myth. In recent years, nothing has fundamentally changed here, in 99% of cases you will come across scammers who will simply scam you for money.
It is sad that this topic is so much discussed today, as if in Russia you can buy data for any person for a small amount. This is a lie. As well as the lie that tens of thousands of people have access to such data. But who cares? Sounds beautiful and fits perfectly with urban mythology.
Related Links
Share:
we are in social networks:
Anything to add ?! Write … eldar@mobile-review.com





