Another test of the speed of the mobile Internet in Moscow. Wireless charging could set your phone on fire? Finally, they deigned to admit that the “social monitoring” was almost more harm than good. Again about telephone spam. The intrigue with the Yandex.Weather application: “… this never happened, and here it is again!”
Mobile internet, who is faster?
This time testing was carried out and the results were published by the resource iPhones.ru, respectively, and the measurements were carried out on “apple” devices. You can read an overview of the results here, it is interesting and quite informative.
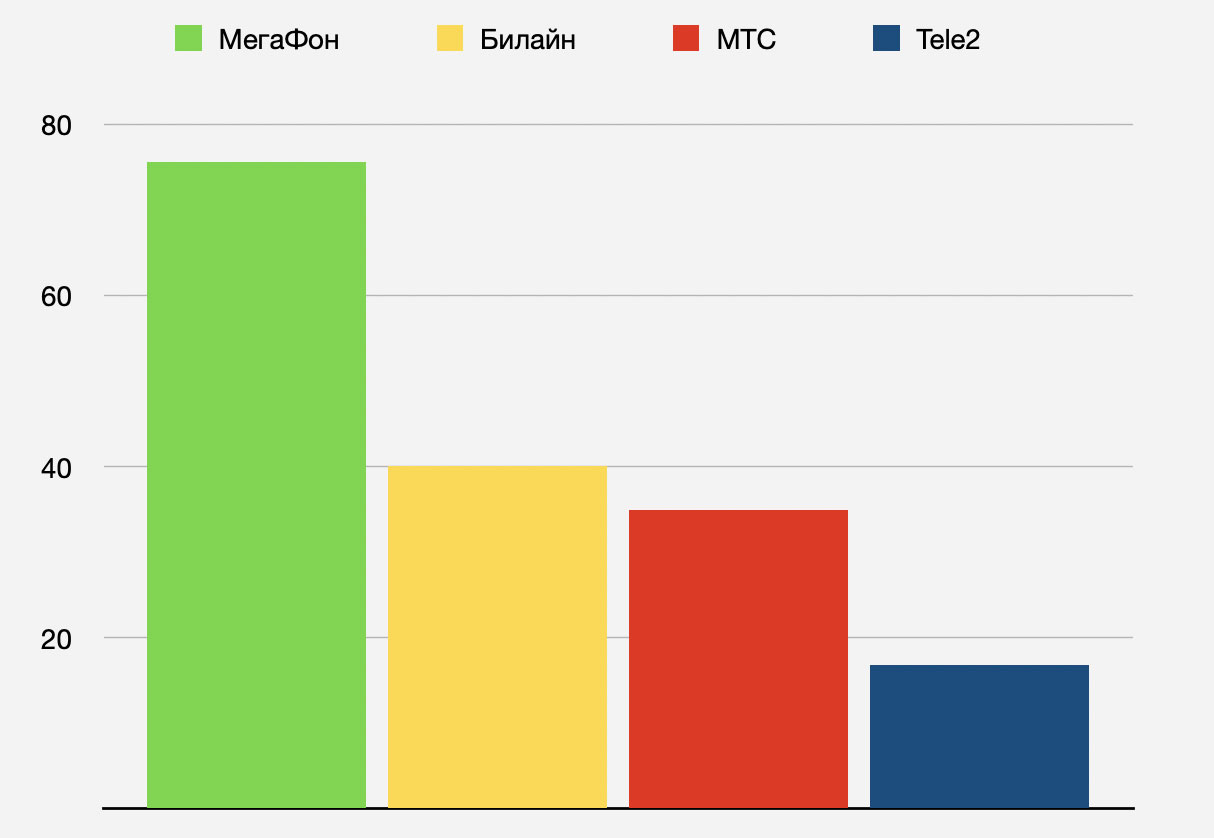
Average operator speeds in Moscow, March 2020, iPhones.ru test
Predictably in the comments, a cheerful discussion of the “engagement” of the Ookla rate and the fact that operators are giving this resource the highest priority, how can you trust such results? As I have written more than once, you can trust the results if you drop 20 percent for your own peace of mind. Once I honestly killed half a day to compare Ookla with a foreign speed meter, the results were different, but not radically. Finally, the most important thing, which I have written about more than once, and the author of the review noted the same: if we are talking about comparison results, then the choice of a measuring instrument is not so important. If only it was the same for all participants.
Well, geography, of course. You shouldn’t be guided by the given figures, too much depends on your location. In general, we are all well aware of all this, but still tend to trust our personal experience more.
It is a pity that they compared only speeds in LTE networks, this puts Tele2 in a deliberately losing position. As far as I remember, the operator has a very narrow frequency band in the Moscow LTE network and the 4G coverage is also noticeably worse than in the 3G network. Therefore, paradoxically, I regularly observed 2G speeds in Moscow Tele3 2-2.5 times higher than in 4G. For the rest – why not compare? For us, in any case, this broadens our horizons and makes the picture of the surrounding cellular world more complete. So let’s say thank you to the guys from iPhones.ru for their work and take note of it.
Roasting your smartphone? Easily!
Fascinating material on Anti-Malware, read it here. It seems that it is technically possible to literally destroy the “enemy” smartphone using the increasingly popular fast charges. We survived, if earlier hackers did a lot of things and continue to get up with software, now they will soon get to the devices at the hardware level. The usual story, the emergence of a new technology that brings people convenience, is always accompanied by attempts to use this technology to bring people in trouble.
In our case, the form of such an attack was called BadPower, a couple of quotes from Anti-Malware:
“… Its principle is to modify the firmware of devices for fast charging, which can lead to ignition of the connected devices. The BadPower vector was described by Xuanwu Lab, a division of the Chinese tech giant Tencent. According to experts, for a destructive attack, it is enough to simply make changes to the firmware of devices to quickly charge. Such devices look like ordinary chargers, but they fulfill their task with the help of firmware that interacts with the connected devices, “coordinating” the charging speed.
The essence of BadPower is to modify the charging parameters set in the default firmware. In theory, an attacker can significantly increase the power, which will damage the connected device: components can melt, deform, and even ignite.
BadPower can be implemented stealthily and very quickly. The attacker just needs to connect his equipment to the device for fast charging, wait a few seconds and ready – the firmware has been modified. “

How scary to live … Now let’s remember how many free and widely available wired chargers for smartphones around us, to keep such is a sign of good form for many enterprises and organizations. If “contactless” fast chargers become radically cheaper, then there will be a lot of them, and, unfortunately, we also have a lot of those who like to play dirty tricks. Defense, of course, will come up. Look, the tenth Android already knows how to disconnect the USB port in case of dangerous heating, you can read a short note here. They will also teach you to turn off the quick charge, if they have not already taught. It’s still somehow uncomfortable, the potential damage is very great.
About “social monitoring”
Recently I wrote about “epic fail” with the application “Social monitoring”, you can read the review here. A wretched piece of work, a part of the program code of which was unobtrusively “borrowed” from a program for tracking garbage trucks developed three years ago. This “social monitoring” was feverishly finished after the launch and the beginning of its forced (!) Use, and in the meantime, the disgusting application was no less feverishly imposing fines of 4 rubles. anyone hitting and it is not clear why. In general, the intensity of indignation reached such a degree that the mayor spoke there, and the Human Rights Council under the President of the Russian Federation demanded an amnesty for all fines.
Read the material of “Interfax” here, many things are called by their proper names, hack – it is hack, and not something else, vaguely called “there were some shortcomings.” Quote from the material:
«»Большинство штрафов, выписанных в период самоизоляции из-за пандемии коронавируса в Москве в рамках работы приложения «Социальный мониторинг», отменены, сообщила уполномоченный по правам человека в столице Татьяна Потяева. Тысячу обращений получил уполномоченный по правам человека, среди них большая часть это по работе «Социального мониторинга», и эту тему мы обсуждали с правозащитным сообществом», — сказала Потяева на заседании Мосгордумы в среду. «Сейчас, вы знаете, большинство штрафов уже на сегодняшний день отменены», — добавила она.
Earlier, the Human Rights Council under the President of the Russian Federation announced the need for an amnesty for administrative fines for violating self-isolation during the spread of the coronavirus.
«Председатель Совета Фадеев предложил отменить в досудебном порядке не только те штрафы, которые были начислены в результате сбоев приложения «Социальный мониторинг», но и все остальные штрафы за нарушение самоизоляции, если эти случаи не повлекли негативных последствий»».
Avoiding fines is good and right, but you need to show consistency and punish developers, no? The application came out frankly lopsided, and the developers demonstrated a complete lack of understanding of how positioning occurs in cellular networks. I went out to smoke on the balcony or went down to the first floor in an elevator to take a newspaper from a drawer – a fine of 4 rubles was punished, how is that? Yes, even in your own toilet, the phone can easily jump to another BS and “get a grenade, fascist!” Should there be some kind of responsibility for the work? I don’t demand to put the developers in jail, these are three fools-girls for the sake of a vidosik stuck out on Red Square in swimsuits and sat down for 000 days. And the developers of the application did not commit such socially dangerous acts. They “just” unintentionally (I hope) tried to steal from Muscovites for 15+ million rubles, and again unintentionally, out of their own illiteracy, greed and irresponsibility, put on the ears of many thousands of city residents. But this is a trifle, right? Okay, let’s not be bloodthirsty, but to get them to return at least half of the million received as a fee for outright hack-work, is that at least possible? It seems that officials are not going to scratch themselves on this topic. If, in the end, no one scratches itself, and the developers happily take away their millions of royalties in their beaks, is it because the offended developers can then demand that officials return the kickbacks received?
Damn coronavirus, sabotaged officials on so many fronts! The Ministry of Healthcare is now overwhelmed by the consequences of their reductions in “unnecessary” doctors and the “modernization” of healthcare that have come out into the light of day, as if in the end it would cost 10 times more than the savings achieved.
About telephone spam
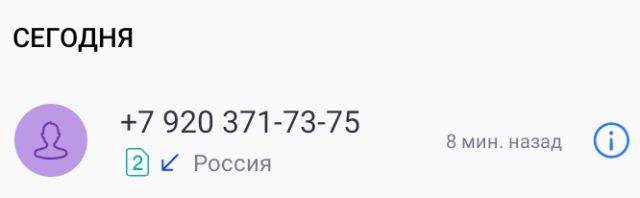
I cannot say that telephone spam “gets sick” so much, on average 1-2 calls per week. Therefore, I treat this philosophically, I am not indignant and I do not take any measures, since it is possible inadvertently to “filter out” an important call. More often than not, they offer to go through a free medical examination, and I guess who leaked this particular database to the network, which was then bought by spammers. There is an opinion that there is no point in answering calls from unfamiliar city phones, they say, probably spam. Apparently, many people think so, because now they are increasingly calling from federal cell phones. Code 920 has come across to me more than once, so I was not too lazy to look at its origin. MegaFon, Ivanovo region. This region is famous among Muscovites for its tariffs: the prices for communication are low, and it is not far to go. They called me on a megaphone number, possibly from a package tariff with an unlimited intranet.
Not everyone is able to talk to a live employee of the spam “call center”, now the first contact is usually with a robot. Further, if you show interest, a live spammer will deign to spend his time on you. Previously, people tried to somehow take revenge on the spammer: they were playing for time (they say, let him pay), shamed, cursed. Now all this is practically meaningless, the call is usually free for the spammer, and the robot cannot blush, and he does not care about swearing. You can, of course, spend time and purposefully get to a living person, but is it worth it? I feel sorry for my time and nerves, I just press the hang up button. How do you react to advertising calls? Tell us interesting.
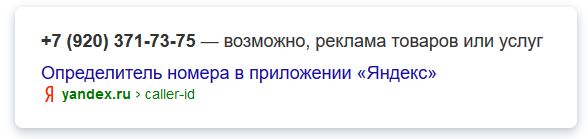
The spam-advertising nature of the number is well known to Yandex, and the operator has probably already received many complaints about the number. Result? As you can see, the result is zero, the number is alive and well and continues to be used for spam. You can try to complain to Roskomnadzor, again if you don’t feel sorry for your time. People praise various free programs that maintain their black lists and block such numbers. Blacklists of cellular operators are probably the freshest and work more efficiently, the call is blocked, even before they even reach the phone. But this service is paid by cellular operators. How do you deal with this scourge? And are you struggling? If programs, then write the names, people will come in handy.
About the weather in Yandex
There is a good Yandex.weather application, I like it. The app itself is informative and the widget is nice. Once upon a time this application stopped working on my smartphone, and I was looking for an alternative, I was surprised to realize that I did not like everything I had tried. Maybe, of course, a matter of habit. However, this is not about that.
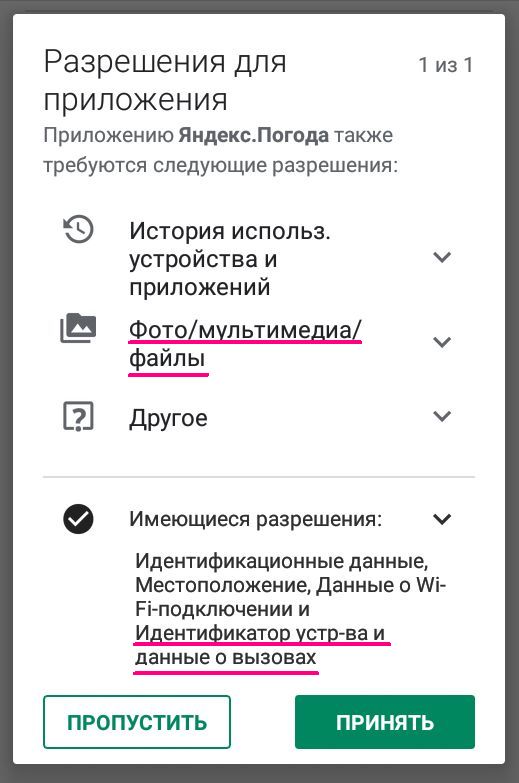
With the next update of the software, she suddenly demanded additional permissions from me, this time access to photo / multimedia and other files. At the same time, she reminded of the previously received permissions, including access to information about calls. I’m not obsessed with privacy and other similar topics, but then I thought: an application whose only function is to show the weather forecast, why would it suddenly need my photos, eh? And why call information? Other permissions can be explained by the implementation of the full functionality of the program, but I did not have enough imagination to explain these two. It would be interesting to hear the official answer from Yandex. To be honest, I didn’t like Yandex.Weather’s curiosity. And, as they say, the question “to the heap”: why does the application climb into the network without asking to update data? In the settings there is a rich selection of update intervals, including “manual only”. So, on at least four different smartphones, I never managed to achieve this “manually”. The application still periodically climbs into the network to update the data, the frequency is different and the algorithm is incomprehensible. Who knows, maybe after each call, he dumps information about him to Yandex, for that he climbs. Most likely, I’m fantasizing, but there must be some kind of rational explanation? What do you say? Your opinion is interesting, especially the opinion of those who used this application.

UPDATE. While the text was slowly being written, a comment came from Yandex, thanks to them. Intricate, of course. Permission to access photos / multimedia and other files solely in case of contacting support? I wonder how they got along all these years without such permission. The second question is also strange. Access to location determination by the application was obtained a long time ago, it turns out that determining the location using data from the base station requires a separate permission, called for some reason “call data”? Or is the Yandex comment – a little pasta on your ears? Or is it a refinement of Google’s policies, which is constantly working on them?
I suspect that the whole bunch of suspicious permission requests, if desired, can be explained for any application, including a screen saver or calculator. What actually happens when scammers embed Trojans into harmless, unpretentious flashlight applications, read our review here. The review was three years old, but I’m afraid that in many ways it has remained relevant.
And another slightly unexpected conclusion. It is possible that there is often no trace of malice and other deceit. Paradoxically, however, the software developers themselves could eventually devalue all these prohibitions and permissions. According to the principle “let it be, what if it comes in handy? In the support there, from the application, write with photo-screenshots, or even some kind of fantasy will suddenly fly into the user’s head. ” And there is a request for access to the address book, sending SMS and determining the location for applications of the “screensaver” category, and this does not bother us at all, we are already used to it. Well, what if all applications require the broadest access rights, then why is the screensaver worse ?!
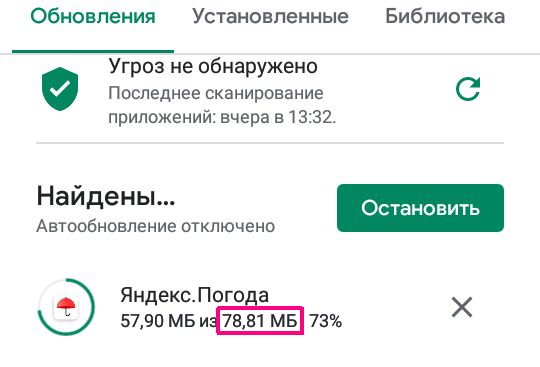
PS A common thing, in the process of writing the material, something else arrives exactly “to the topic”. I don’t know how or why, but the phenomenon really “takes place”. Today the Yandex.Pogoda update has arrived again. Auto-updates of software are always disabled for me (bo nefig!), So I saw it willy-nilly. Good people, 80 megabytes is an update to the program that displays the weather forecast, nothing more! Moreover, the program takes this forecast from the network every time, and does not calculate it itself. What can be updated there in such volumes? Inline ads? So an office suite for a smartphone weighs less, even together with all its advertising “hinge”. Inevitably, you start to think. It’s good that I really have nothing to hide and I’m hardly interested in Big Brother.
Related Links
Share:
we are in social networks:
Anything to add ?! Write … eldar@mobile-review.com





