Hey.
Data security remains a thing in itself for most people. Until the thunder breaks out, no one will do anything. And this manifests itself at all levels, without exception, someone has this indifference about their phone, someone does not protect the computer. Thunder struck in Belarus, and the number of those who have rapidly mastered VPN clients has grown. I wrote about what you can do to bypass the locks in a separate text. There is no sense in returning to the topic of Belarus now and within the framework of Biryulek, read the article about blackouts.
And we’ll kick off with last week’s key theme, Epic Games’ corporate war against Apple and Google, let’s go!
Content
- Epic Games vs. Apple and Google, their own rules of the game
- Russian SIM-cards for crime bosses all over the world, inexpensive!
- VoLTE is hacked and your calls can be easily intercepted! Instructions on how to eavesdrop on other people
- Voice spam, new peaks of the past week
- Sometimes They Come Back – Google Travel Service
- Our dead return to Telegram and other messengers
- Vulnerabilities in Qualcomm processors – old and new, 400 pieces
- Some photos from Galaxy Note20 Ultra
Epic Games vs. Apple and Google, their own rules of the game
Epic Games’ war against Apple was a striking event, in which Google was quickly involved, acting on the side of Tim Cook’s team. Let me remind you that during the hearings in the US Congress, attacks on Apple were related to the iOS app store. Apple can set any prices there, but the main thing is that you can get into it only through moderation from Apple, and there are simply no alternative ways to be present on the company’s devices. Therefore, Apple 100% controls applications for its system, can refuse developers without explanation, discriminate against them in various ways. There was a separate text about the Congressional hearings, this is the best humorous show of this year!
– Do you really eat children?
– No, what are you talking about, I only eat children when I’m very hungry!
– Are you often hungry?
– I believe that this happens to me.
– So you eat children?
– I find it difficult to answer this question, I need to clarify this point.
Read the text about these hearings, many of the questions will seem interesting to you.
The attacks on Apple are government-sanctioned, and there is a growing confidence among developers that the corporation will not resist, the rules of the game will change. This is indicated by many events, for example, in Russia, the company agreed to preinstall the applications of local companies from January 1, 2021, this has never happened. There is a feeling in the market that you can force the company to change, and then, you see, the approach will change, and there will be the possibility of the appearance of alternative app stores or installing applications bypassing Apple.
Epic Games are keeping their nose to the wind, the company decided to kill several birds with one stone. To begin with, Apple was lured into an ambush organized according to all the rules of the battle. Epic Games has created an in-game currency for Fortnite – V-bucks. This virtual money can be bought for real banknotes, further in the game you buy certain items. Why does the company need an in-game currency? The answer is obvious – in-game sales bring significant money, but today you need to give part of the payments to the platform holders. For example, Apple receives 30% of such payments for a great living. And the solution from Epic Games is somewhat elegant, they bypass the written rules. But how correct is this? Of course not, Epic clearly understood that their game would be blocked and prepared for this. In a matter of hours, Apple removed the game from the app store. And then a prepared blow followed.
To begin with, the cult video Apple – 1984 was taken. It will be useful to remember it.
And then Epic made their own video, only Apple is now playing the role of the tyrant, it turned out nicely and quite truthfully.
In parallel with this, the company filed a lawsuit that Apple uses vicious business practices. An important point to be considered in court is that Epic Games is calling Apple a monopoly on its own iOS platform. You have no way to bypass Apple’s moderation, there is no way to get into devices in any way without Apple’s approval and those payments that the company unilaterally establishes. And this in many ways turns the whole situation upside down. Until recently, Apple fought off antitrust authorities by pointing out that they did not dominate anywhere in the world. The share of iOS devices is quite low, and this made it possible to avoid problems. Epic Games’ message does not dispute this, but the key point is that there are no alternatives to the App Store in the app store market, and it is 100% controlled by Apple. If the court accepts these arguments, then we will see an epic battle when Apple has to create a mechanism to independently install applications on iOS. It is impossible to expect the court to be fast, it will take years, as it usually happens.
Curiously, Google has also removed the app from the Play Store, but Epic isn’t a problem, you can install Fortnite from Samsung’s app store or directly. A lawsuit against Google has also been filed, and now there will be courts. Epic Games has enough resources to make both corporations pay high costs for their business practices.
But there is still Spotify and other equally notable companies, a wave of claims against Apple and, perhaps, Google will only grow, not the time to forgive this or that money. Corporations will force them to moderate their appetites, to make them smaller. As for me, this presentation is correct, since we, as users, will pay less.
I’m really looking forward to seeing many services start running through web browsers, this is the hottest topic of the year. For Apple, this will mean the need to either block such services (all payments, everything past their store), or put up with it. Something tells me that they will not be able to put up with the company and will figure out how to put a spoke in the wheel. But let’s not get ahead of ourselves, this is a very interesting moment.
Russian SIM-cards for crime bosses all over the world, inexpensive!
Demonization of Russia in many countries of the world is in full swing. Who Intervened in the US Elections? Russians. Who is going to overthrow democracy? Russians! Who is building military bases around the world? Russians. Propaganda has long surpassed the times of the Cold War, when, after all, there were some limits and restrictions, today there are no more brakes.
Vice has an article about “Russian SIM-cards”, where creativity and invention reach an extremely high level, and the described phenomena are confused to the point of disgrace. The original text can be found here.

I was surprised to learn from the article that “Russian SIM-cards allow” to do the following:
- Fake numbers when making calls, the phone will show the number that you typed in, or the name, for example, of your bank;
- such SIM cards are not tracked in any way, they may not have a number, and then they are used for anonymous data transfer;
- Russian SIM-cards allow you to change the voice of the caller, for example, the voice of an adult is turned into a child.
It’s time to remember what a SIM card is. This is a module for identifying a subscriber on the network, there are no functions inside the SIM card for voice substitution, moreover, the technical capabilities do not allow this. Motherboard Vice discovered the existence of GSM gateways, and they are at least two decades old. Such gateways make calls for you, you only need to register their data, pay for services. And scammers all over the world fake calls in this way, they substitute arbitrary numbers or indicate bank numbers and / or their names. When you receive a call from your bank and his name glows on the phone screen, then trust involuntarily arises. After all, scammers couldn’t fake the name on the screen, could they?
The new wave of old technology now includes the sale of SIM cards that are configured to work with specific gateways, this is an easy way to develop an old service, a slightly different marketing. Such SIM cards work anywhere in the world, you just need to correctly set all the settings (SMS center, APN, and so on). The principle of operation is similar to travel maps, there are no differences. But, as before, calls go through some African server, usually GSM gateways are located in that part of the world. But the name “Russian SIM-cards” arose from the fact that someone in our country was the first who tied such cards to gateways, showed the service from a slightly different angle. Happened!
Inside Russia, the use of GSM gateways is illegal (for such purposes at least), so they are located outside the country. Since fraudsters widely use them, operators block the operation of certain gateways in order to limit the opportunities for fraudsters. It’s a long, tedious job. It’s like you pick mushrooms every day after the rain, which does not stop and the end and end is not visible to it.
Since the calls go through the gateway servers, additional software can be installed there, for example, to change the voice. This is not the merit of the SIM card, but the software on the server. And there can be many such software modules.
These SIM-cards do not and cannot provide any anonymity. Moreover, in any country in the world they are like a beacon, attract the attention of both the operator and law enforcement agencies, they are too easy to spot on the network. As well as receive all traffic from them, calls, and so on (all transmitted commands are visible). I know examples of how states have installed such GSM gateways on the territory of third countries to collect intelligence information and receive operational data. There were several such companies operating in the Baltics about ten years ago, they massively collected dirt on their users and what they were trying to do. In those stories it came to blackmail, extortion and other pleasant “little things”.
The phenomenon itself, described in the article, has nothing to do with SIM-cards and any of their magical properties. You can call the GSM gateway from anywhere. It is possible that some gateways require only their own SIM cards to work, which are registered in the system. But these are already details. It is important to know that this is not something new at all, not something unusual. The phenomenon has existed for a long time and is well known. The thing is dangerous for the user, since the very use of gateways attracts the attention of certain people, law enforcement agencies.
VoLTE is hacked and your calls can be easily intercepted! Instructions on how to eavesdrop on other people
Academic research is often described in the media, which, either due to misunderstanding or for some other reason, turns ordinary work into something sensational. Such a sensation was the possibility of intercepting voice calls via VoLTE, which was discovered at the Ruhr University (the town of Bochum, there was once a Siemens production, or maybe it was Bocholt? Everything was erased in twenty years – rather the second).
So, the attack was called ReVoLTE and was even described in great detail in a separate article, you can find the original here.
In order not to go into the wild, I will reduce everything to a very simplified explanation. VoLTE calls can be intercepted and subsequently decrypted. To do this, little is needed, for example, special software and a device for scanning the air (sold in every household!), Knowledge of the sector of the base station from which the subscriber is calling, and its location (you cannot move), as well as such a trifle as two calls, that go in a row. Since the first time you intercept the encryption keys, and the second you do the decryption. And the subscriber must not move, plus you must know his number!
The reason for hacking is that one of the providers of infrastructure equipment did not enable by default the setting in the software (in the checkbox parameters) so that a different encryption key is issued for each call. For the vast majority of vendors, this is the default setting, that is, the ReVoLTE attack is basically impossible. Researchers examined 15 options for operator equipment in Germany, and found vulnerabilities in 3 cases. And they concluded that in many countries such an attack is possible in the real world. Moreover, they demonstrated interception by their examples (knowing the number, location, and so on, that is, they made the task as easy as possible for themselves).
The problem of intercepting VoLTE in this work is not in the vulnerability of the networks, but in one configuration parameter, which the negligent operators did not enable, but the provider disabled by default. I checked in Moscow and St. Petersburg the possibility of such an attack on the networks, none of the base stations of different operators turned out to be susceptible to it (or maybe I was not lucky). As a speculative exercise, this study is quite interesting, but one must understand that it stems from many assumptions and not a minus in the network architecture, but simply a disabled setting on the part of the operator. This is about the same as turning off the antivirus on a computer, and then deliberately infecting it with a trojan and then writing a study that there is a threat and it is serious. After all, if you disable the antivirus, the infection of your computer becomes possible. It so often happens that the headlines and descriptions of articles turn into sensations, which in practice are not worth anything.
All the time I remember the same kind of PR of a Russian company that deals with network security and finds vulnerabilities in the signaling network at the international level. The description always looks very simple – you take your access to the network and then do this and that. They just forget to add that it is impossible to get such access in practice. This is akin to the advice “take a nuclear warhead from a warehouse so-and-so, it definitely lies there.” Therefore, my attitude towards these sensations has not changed, they are very far-fetched in most cases.
Voice spam, new peaks of the past week
Either there is a crisis, or something has happened in the heavenly realms, but there is an indecent amount of voice spam. I decided to count the number of such calls last week, on Sunday I knocked up the total and was stunned:
- On MTS – 14 calls (blocked in the software as spam 4);
- Beeline – 9 calls (2 blocked);
- MegaFon – 12 calls (3 blocked);
- Tele2 – 17 calls (fresh SIM-card, so I think that all calls are spam, the phone was just lying there, but perhaps it was not spam, I can’t judge here. The number is new).
In the first place – the language school of heavenly English, in their opinion, my number was given by one of my friends. None of the calling girls could answer the question, what is my name. They offered discounts, trial lessons, lured them in every possible way. I signed up wherever I could and brought all my friends. I immediately sent the numbers to spam. Please note that the girls called from cell numbers (I checked, these are real numbers). In one of the calls, as a key client that he is ready to bring the whole company for training, the girl got into a conversation. They sit at home, this is a third-party company for calls, calls are made by the program, there is software on the computer. Speak through a headset. Payment for working hours plus bonuses for brought clients.
I was pleased with Rostelecom, because when asked where they got my number, the girl cheerfully read out a prepared speech: “We use a program that selects numbers randomly, and so we call you.” The restrictions of the law were not very elegantly circumvented, but they were circumvented. I listened with pleasure to the proposals, dictated the address where I want to connect the Internet of this company. I can share with you: 6 Exhibition Street, London, UK. What, they don’t connect? What a pity! But call again, I’ll be glad to talk.
And yet they often start a conversation like this: “I have an offer for you, are you ready to listen to it?” You answer – you’re not ready. The girl begins to chatter the memorized text.
On Saturday night, I was pulled out of a boring Belgian pub with a glass of cider in the company of friends by some kind of polling service. There, the aunt was alive, but she was imbued with the grandeur of the moment. At 10 pm Saturday, she wanted to hear what we thought about some events. Everyone shouted into the phone, but for some reason she passed out, saying at the end that they have a serious organization, and we are all joking. The number also went to the spam list.
Friends shared their painful concerns, they also had a lot of spam calls, as if in recent weeks Pandora’s box had opened and someone had mastered telemarketing. Therefore, the proposal for a new car was perceived by me in a completely different way, at least something new. While driving, we discussed a budget foreign car, different options for installments, the choice of salon and whether there is such an option. If you need to know something about a budget car, then I learned more in half an hour than in previous years. A very interesting conversation, you need to extract something useful from everything. Our conversation ended amusingly: “Everyone hangs up, yells at me, and it was nice to talk to you, although I understand that it’s useless.” An intelligent person, nevertheless, realized and, nevertheless, got distracted and chatted about something that way, uplifting.
Oh, I completely forgot to say about legal aid. They were also active. And there was also Sberbank, from there they called from the security service (scammers, of course). Even without answering calls, but simply being distracted by them, I spent enough time and attention. And now I understand why many of my acquaintances have disconnected the call for unknown numbers, do not pick up the phone. Since the operators do not struggle with this, everything is in our hands to prevent spam from getting through. Do not forget to add the calls of these spammers to the spam list, make it difficult for them. Each platform has software for monitoring spam calls, somewhere such utilities are built into the system.
Sometimes They Come Back – Google Travel Service
I loved the Google Travel app, but it was mercilessly killed last year for unclear and vague reasons. In a world ravaged by a pandemic, expecting Google to revive this old story was difficult, but the company did it. The same service has appeared at travel.google.com – your reservations, flights and ticket searches, places that you can visit in the selected city.
At first glance, little has changed here. Added a link to news about COVID, the number of cases. For Russia, statistics for the country, for individual cities, it is not shown. Or they didn’t show me when I tried it.
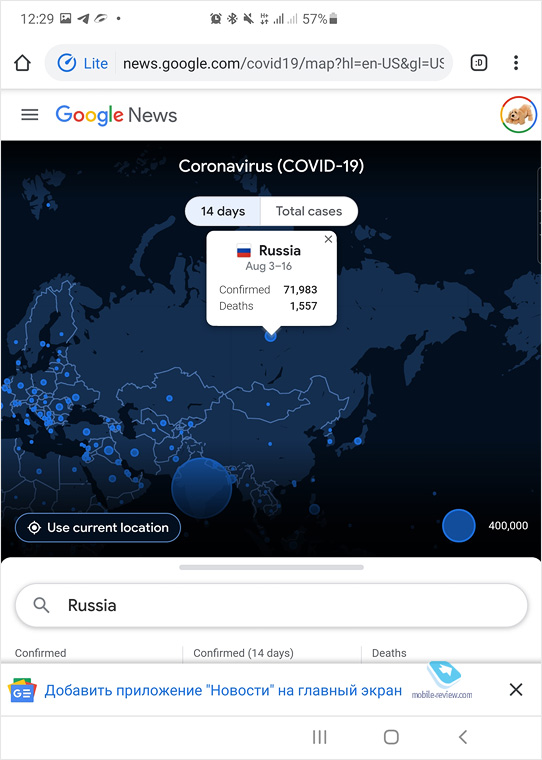
At the moment, the service is not localized, there is no Russian language. But I think that since Google has decided to re-launch Travel, then localization will not be long in coming. There is no separate application, it is not known whether there will be one. But the good news is that Google is optimistic about the future and believes that soon people will start traveling as before, which means that such a service will be in demand.
Our dead return to Telegram and other messengers
About six months ago, Eldar Murtazin appeared on Telegram, about which my messenger happily informed me. In the photo there is a teenage girl, she has my old MTS number.
It turned out funny and somewhat unusual, the old issue got a new life. Since my business card with this number was not correct, hence the signature, it is taken from the phone book. But when it’s your number, there is nothing of the sort. What if this is the number of your friend who died? Somehow I didn’t raise my hand to erase these numbers from my notebook, although quite a long time had passed. And now Telegram writes to me: such and such appeared in the messenger. I understand that this is another person who took this number, and he does not even know that someone used it before him, what kind of person it was. But a chill runs down my spine, as if the dead could return.
I thought about the fact that once the guys, leaving on distant business trips, associated with risk, wrote letters to their mothers, and their colleagues sent them week after week. But return letters did not reach, the mail “lost” them. After the business trip, the guys were waiting for envelopes with letters that they read. If you look at modern technology, then everything may be different. Communication in the messenger can be conducted by a trained AI bot, open your chats, they are often monotonous, built according to the same algorithm – hello, I’m fine, like you. And such programs will become much smarter, for some it will become an opportunity to keep in touch with a deceased relative. People will understand that this is a simulacrum, something artificial. But it will be at least something. And similar developments are already being carried out by several companies to provide a virtual you for relatives. As usual, the military will be the first to experience it firsthand. Chat for loved ones who will not be told that this is just a chat with the program. A kind of series of “Black Mirror” that becomes reality. Goosebumps are creeping up from this, the virtual world offers effective surrogates of reality, into which you can escape from pain and bitterness. This seems to me to be a very dangerous technological development that can cut not only the lives of individuals, but also society as a whole. What do you think of this virtualization of the dead? Do you need it or not?
Vulnerabilities in Qualcomm processors – old and new, 400 pieces
The incredible happened, the research company Checkpoint published a note in its blog, in which it describes the vulnerabilities of all processors from Qualcomm, without exception. It is noted that there are 400 of them, and most importantly, they allow you to receive all information from smartphones – user data, including photos and videos, correspondence, and so on. Or you can just block the device. Or install your own software, which you will never see. In a word, get full and unconditional access to your smartphone or tablet.
The note can be found here.
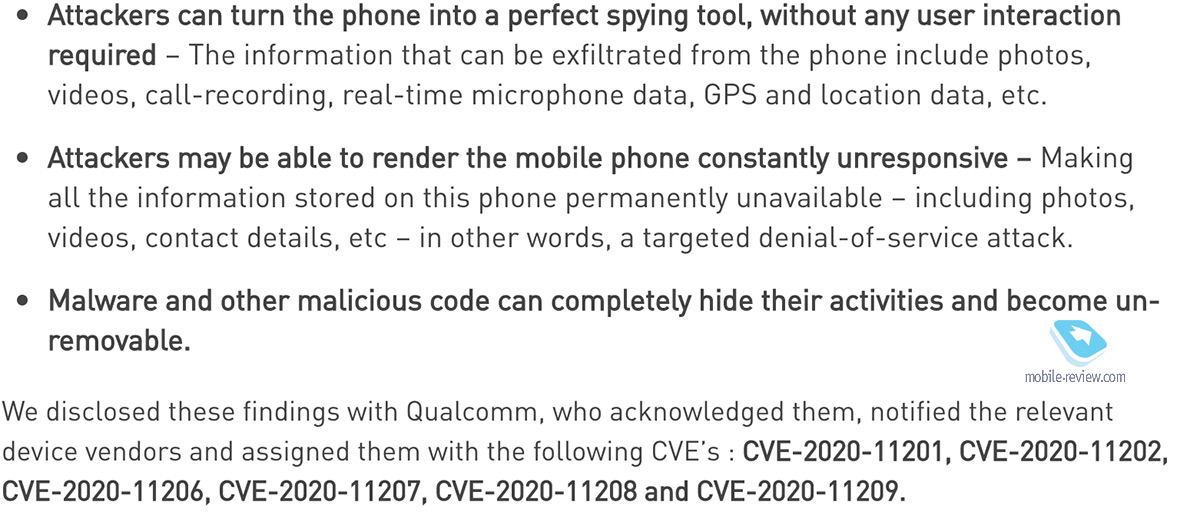
There are no exact descriptions of the vulnerabilities, but Qualcomm has been notified, the numbers of incidents are given that they have already received fixes, and vendors must add them to the code. The number of four hundred vulnerabilities is striking. That’s a lot. But perhaps something is not very applicable in life, something is secondary. However, this is a lot.
Pondering this story, I immediately discovered analogies in Qualcomm’s behavior with that of Apple. Errors in the code allow you to secretly remove data from devices, you do not even need physical access to them (and here is the code of the processors, including the DSP). It looks like a back door that was left on purpose (but no one can formally blame it), and whoever needs it has access to them. One fact speaks in favor of this version, in America it is forbidden to sell any devices based on processors other than Qualcomm or those created by Apple. You cannot certify or sell smartphones on anything other than Snapdragon. So much for the open market. What Checkpoint describes fits well with this market feature. With the tools to spy on any device, there is only one thing left to do – to ensure that 99% of all devices are available to you and no exceptions have happened. This version is beginning to acquire more and more circumstantial evidence.
And here we come to a question that has been embarrassing me for a long time. Why in a number of countries a company started against Exynos and for Qualcomm, why does it coincide in a number of ways with how we were told about the harm of 5G and base stations of this format. This is being discussed not only in Russia, but also in a number of other countries, with the exception of China. I think that you will find the answer above, although I do not like conspiracy theories, they can explain anything. The gradual growth of Qualcomm processors in South Korea fits well into this canvas, the closest partner of the United States by hook or by crook is trying to achieve the same situation as in its home market. But this is hardly possible for many reasons. Interesting times, interesting pieces of information appear in our field of vision.
Some photos from Galaxy Note20 Ultra
A review of the Galaxy Note20 Ultra will be released this week, but for now I want to share a small number of photos, I think they will show well what the camera can do and how it shoots. In our Telegram channel, I asked to rate how the pictures looked, the majority thought they were good or excellent.

And here are the pictures for those who do not watch our Telegram channel (I advise you to subscribe, it has become much more lively and interesting there).
PS Have a good week to get things going. Subscribe to the Telegram channel, you can do it right here – it’s lively there.
Let the sun shine brightly, and nothing bad happens to you or your loved ones. See you!
Back to content >>>
Related Links
Share:
we are in social networks:
Anything to add ?! Write … eldar@mobile-review.com





