
An ITC.UA reader named Taras (@PhishingAbuse) shared with us an excellent article about phishing in modern Ukrainian realities. We publish in the “Blogs” and recommend reading, although certain knowledge is required to understand everything that happens.

Once, in the comments on Telegram, I noticed that the frequency of fake payments (UN, Unisef, Red Cross, etc.) has increased and I was interested. I remembered that a friend used certain tools to steal a couple of $k from Russians for the Armed Forces of Ukraine, and I thought I should use my abilities, and here is an opportunity – to save money for Ukrainians who do not know what phishing is. Before that, I tried to help everyone in the @stopdrugsbot bot, but later it dawned on me that the effectiveness of this is close to zero.
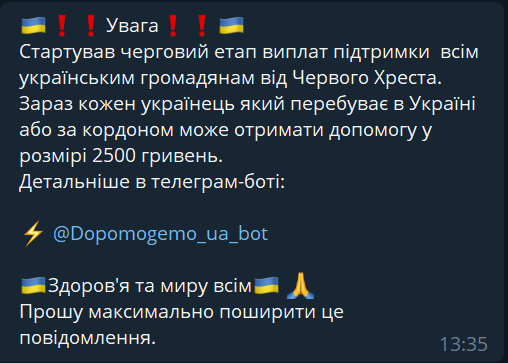
Comments that got everyone
Realizing that user bots (spammers in the comments) do not live long and you need to find the most effective way to cover up, or at least limit, this shop of unprecedented generosity, I began to look for methods – follow all links, count, store. Userbots disappeared, there were a lot of bots, even under one username, but there were few domain names.
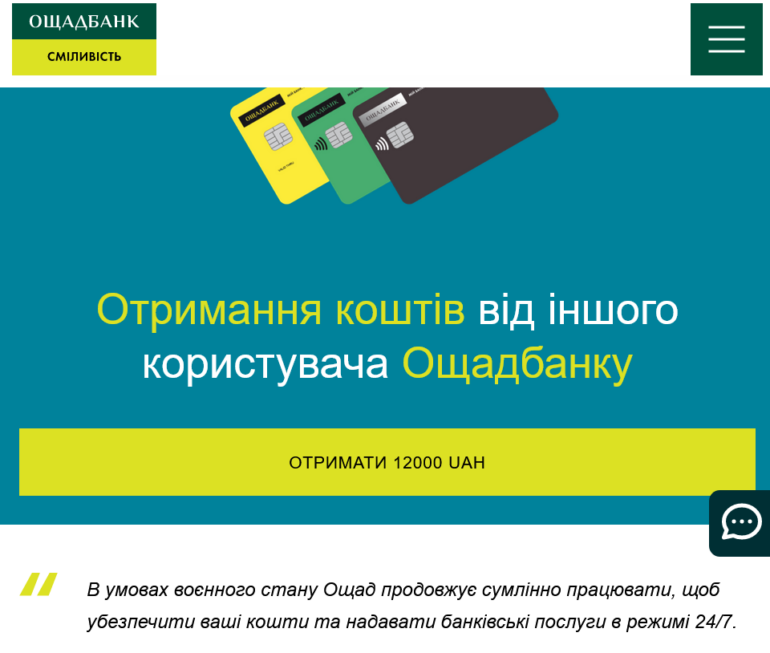
Enticing Page Example
I remembered about abuse contacts for each IP in RIPE – this should work. Then it began – whois by IP gives us Cloudflare – found a form, wrote. Whois by domain name gave only a hint about the registrar – wrote. And after a few hours this site stopped opening. Then it began. He boasted to his colleagues – one said cool (he was also tired of it). We began to search, exchange, immediately give a link to abuse forms. I asked the moderators of a certain channel, where we saw it, if there was something like this recently – they dropped it, it flew away. The correspondence was no longer purely working, and chaos began in the chat.
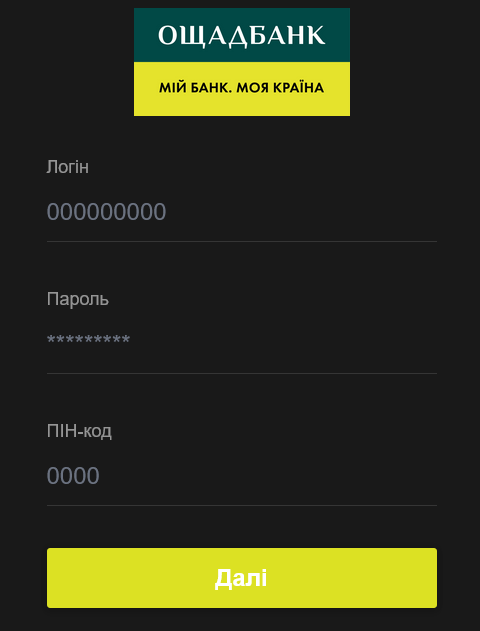
What does saying goodbye to money look like?
When there were more domains and bots, and some were lying, then I already thought that it was time to streamline this matter. I created a channel, wrote a brief instruction, started keeping a list, invited a colleague as an admin. Since the constant annoyance of the moderators does not always give the desired result, I went to the admins, came back with the initial result, and here one of them gave the admin panel. At that moment, it was ideal – you immediately delete messages with a report from the group – the user bot gets almost 100% banned, and also constant access to the history of deleted messages – that’s where all the bots and domains are. Then he asked for another one, although there were fewer spammers there. Our speed of reaction grew, the list was replenished. However, the blocking time varied – from 1-2 days to a week.
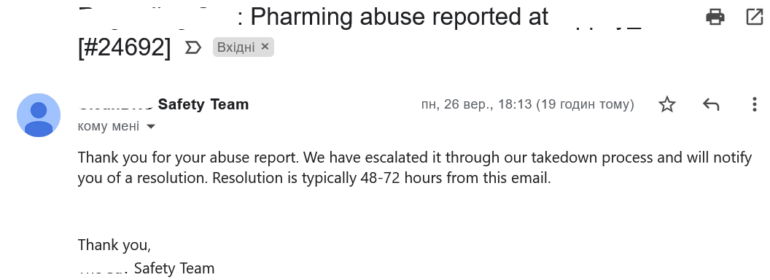
Answer from one of the registrars
However, we were surprised that one of the registrars did not react at all to any letters to all available addresses. Even to administrative contacts regarding the top-level domain. Although everyone else reacted, if not by letter, then by quick actions (even rig-ru takes the domain in a few days, maybe up to two weeks, but I still write to them in English). I even wrote a letter to ICANN regarding that registrar, however they threw up their hands because the country level domain(s). Then I realized that blocking such sites by the regulator is not such a bad idea, despite all the negativity. But it still kept bugging me. Then I found such a tool for us as Google Safebrowsing, because it is quite easy to use – follow the link, enter the full link, specify what needs to be done if necessary:
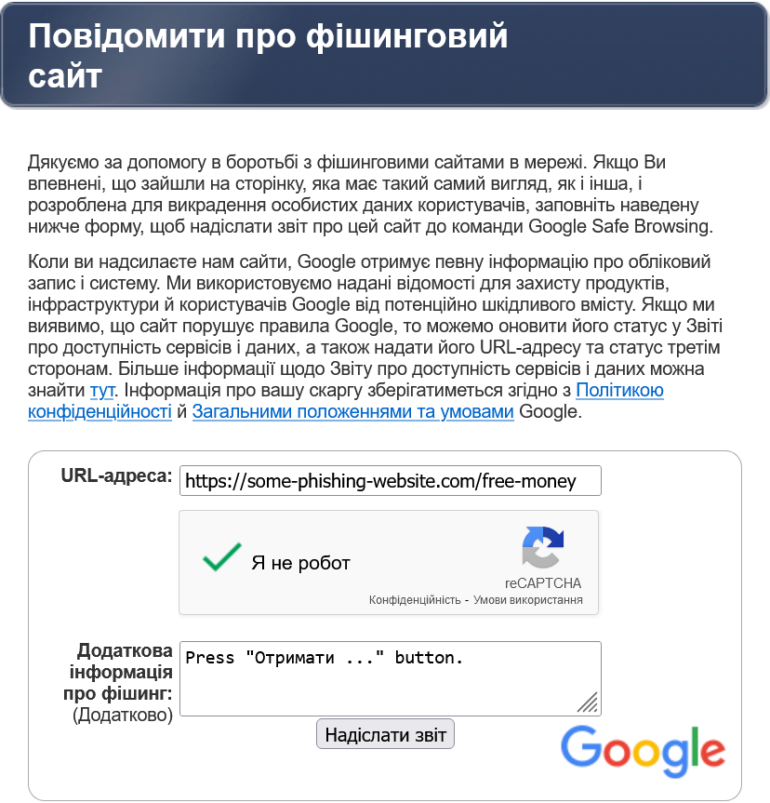
Google Report Form
We choose services that work for everyone, regardless of OS or browser, PC, phone or tablet. And with a sufficient number of complaints with different links, they give such a warning about the domain that it looks unambiguous:
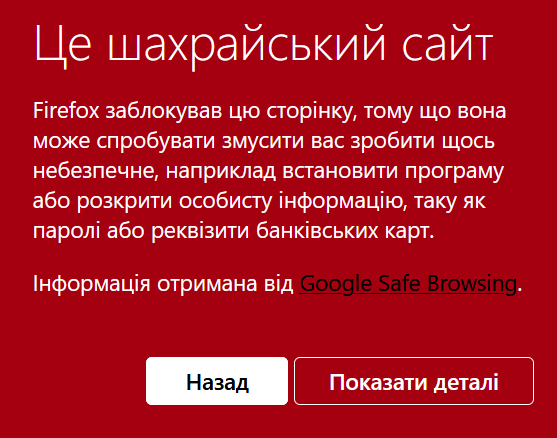
A warning that can’t be ignored
This helped us, because Cloudflare, despite numerous complaints on the link, rarely or slowly helped. But this also happened:

Want when they can
When we read the news that the authorities were catching a little bit of such freaks, we understood the importance of our volunteer hobby, and the list of domains went into the 4th decade, we both thought about one thing at the same time – CERT-UA. At first I wrote an appeal on the site, but I was not sure that it was really accepted, so I duplicated it in the mail: a list, methods, links to the channel and an invitation to cooperate. Even then we knew that it would help both. And they answered – they provided a dozen more bots. Since then, we have been exchanging finds and mechanisms.
Over time, even blocking a domain in problem areas became fast, and against the background of the fact that itc.ua stopped opening due to the excessive responsibility of one of the operators, I also got a burning desire to at least improve the mechanism for blocking such resources by orders from the NCU / NKEC. I wrote a couple of letters to the NKRS to block such domains only at the DNS level, because blocking the IP Cloudflare CDN does not lead to anything good (except for itc, some Uman school and hundreds more domains also suffered). Added this paragraph in the next listing update for CERT-UA. I’m not sure if this helped, but literally in the next leaked order to block harmful domain names, an important clarification was added – on recursive DNS servers. Of course, when I saw the applications, I realized which part we do and which government services. They are great.
However, somewhere the word takedown caught my eye and I started looking for mechanisms or services that will speed up this process (at least for banks), and for which you don’t have to pay. That’s how I stumbled upon Netcraft. Actually, their takedown is also exclusively for clients (over time, I learned that their clients are two large banks), but they had one advantage. After all, we are ordinary users for Google Safebrowsing, and they are probably partners. Therefore, Google always accepts complaints from them. This sped up the decontamination process by a matter of hours, if you’re lucky. However, the automated system of this service in most cases does not find problems, so you need to pull a real person.
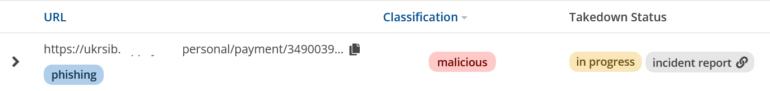
Good news for us from Netcraft
Recently, we have felt that we are not getting enough domains, given the block lists from the NCU/NCEC. I tried to join the largest channels in Ukraine – even almost a millionaire did not have as much as one of those that I saw at the beginning. But when I got to the last ones in the top, I came across one moderator who created a bot that blocks the messages themselves. Of course, this is not a panacea for FB / Vibers, but he pulled a list of links from the database and after the analysis I was a little proud of us – we did not know about only one domain. But he also gave much more valuable data – access to the group where all messages deleted by the bot are sent. It’s perfect. New leads are guaranteed every day, and only the ones you need.
Also recently, the administrator of the “problem” registrar probably got out of a binge / vacation, and now this gives us a reason to laugh. If earlier the domain was registered and launched in the morning, then after the detection it was already “lying” after lunch. Currently, for four domain zones, the site can be disabled after a report in five minutes!. It’s even faster than they run it.
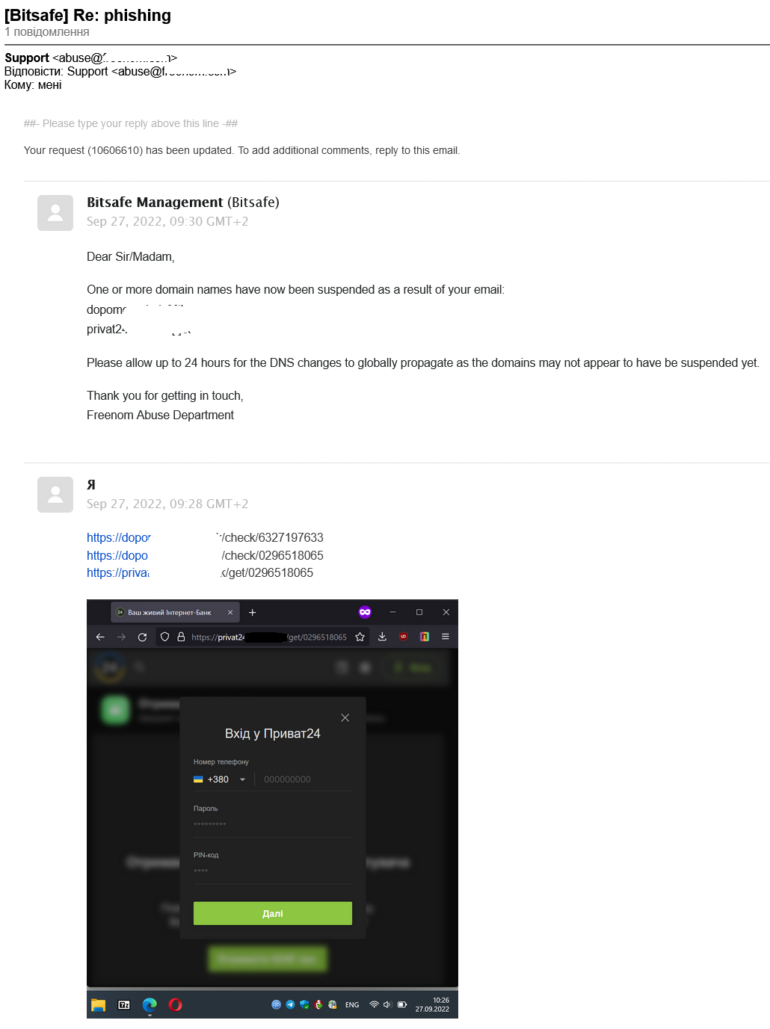
Chain letter from one of the registrars (fast and decisive response to our complaint)
But we also have not without problems – the weekend. Almost all registrars, Cloudflare, Netcraft, do not work on weekends, and therefore the domain registered on Friday evening will probably live until Monday until reports are sorted out. However, our list is about to be replenished with the 100th neutralized domain, and given the tens of millions of hryvnias that will remain in the wallets of fellow citizens, this is a good reason to rejoice. Volunteering can also be like this, there is more than one front and this is a good addition to donations for the Armed Forces of Ukraine.






