Criminals continue to use the problems of mass concern of Ukrainians to spread malicious software. Specialists of CERT-UA recorded a mass distribution of e-mails speculating on the subject of “Kyivstar” and the SBU.
Yes, letters about “Debt under the Kyivstar contract” will begin to be sent to the e-mail boxes of Ukrainians. They have an attachment in the form of the “Subscriber’s Debt.zip” archive, which contains a password-protected archive of the same name. In the latter, there is a document with the macro “Subscriber Debt.doc”. When activated, the macro code will download and run the GB.exe file. This is an SFX archive containing a BATCH script to download and run the wsuscr.exe executable to run the RemcosRAT remote control program.
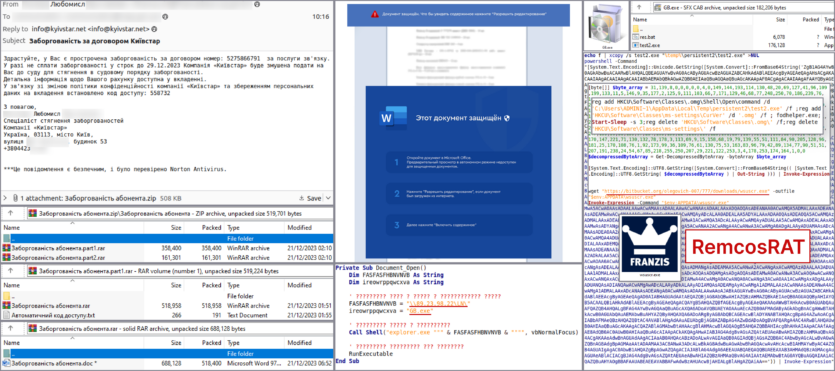
At the same time, CERT-UA recorded the distribution of letters with the subject “SBU request” and an attachment in the form of a “Documents.zip” archive. It contains a password-protected RAR archive “Zapyt.rar” with an executable file “Zapyt.exe”. Opening the archive and running the file leads to the infection of the system with the remote access program RemcosRAT.
CERT-UA experts note that in addition to the typical UAC-0050 placement of the RemcosRAT control servers at the technical site of the Malaysian hosting provider Shinjiru, they are also located within the autonomous system AS44477.
CERT-UA specialists recommend filtering e-mails with password-protected attachments (both archives and documents) at the level of mail gateways.




