Specialists of the government emergency response team of Ukraine CERT-UA, with the help of Trendmicro, investigated a series of cyber attacks aimed at servicemen of the Armed Forces of Ukraine.
Suspicious activity was detected by Trendmicro specialists at the end of 2023 and reported to CERT-UA. During these attacks, attackers, under the guise of recruiting for the 3rd Separate Assault Brigade and the Israel Defense Forces (IDF), sent messages with malware on the Signal messenger. Such messages contain archive files, the launch of whose contents leads to the infection of the computer with REMCOSRAT and REVERSESSH malware. At the same time, the attackers try to make the names and content of the archives interesting for the military – interrogation of a prisoner, geolocation, coding commands, callsigns, etc. Detailed information on the technical side of the attack is presented on the CERT-UA website.
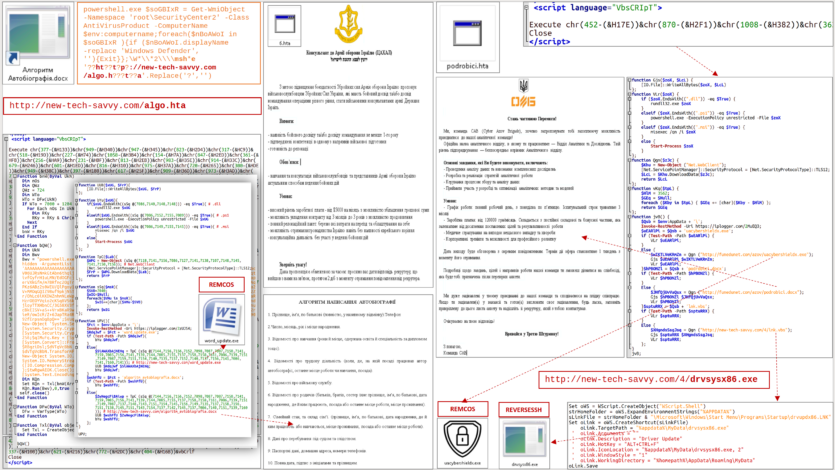
Despite the use of publicly available tools (which may lead to the identification of similarities with other attacks), the described activity by other specific features is a separate cluster of cyber threats and is tracked by the identifier UAC-0184.
CERT-UA reminds that in case of detection of suspicious activity on the computers and information and communication systems of the Armed Forces, it is necessary to immediately inform the Cyber Security Center of the ITS (unit A0334; email: [email protected]).




