
Hackers of the Head Mare group got hold of the servers of the Russian military company NVO Vysokotochni systemi i tekhnologii, a part of the Kalashnikov concern, and posted a lot of documentation on the network. In particular, it includes a description of two types of missiles.
Data on the responsible personnel and their activities, plans of the premises and much more have also been made public. Hackers note that despite the company’s massive cybersecurity efforts, which are mentioned in the documentation, they were able to carry out the breach without any difficulty.
1/7 Hed Mare came to visit the NGO “High-current systems and technologies” from the city of @Izh_govyaku hit #Kalashnikov. We have classified weapons documentation and employee and supplier information pic.twitter.com/eulsgZvpDV
— Head Mare (@head_mare) February 17, 2024
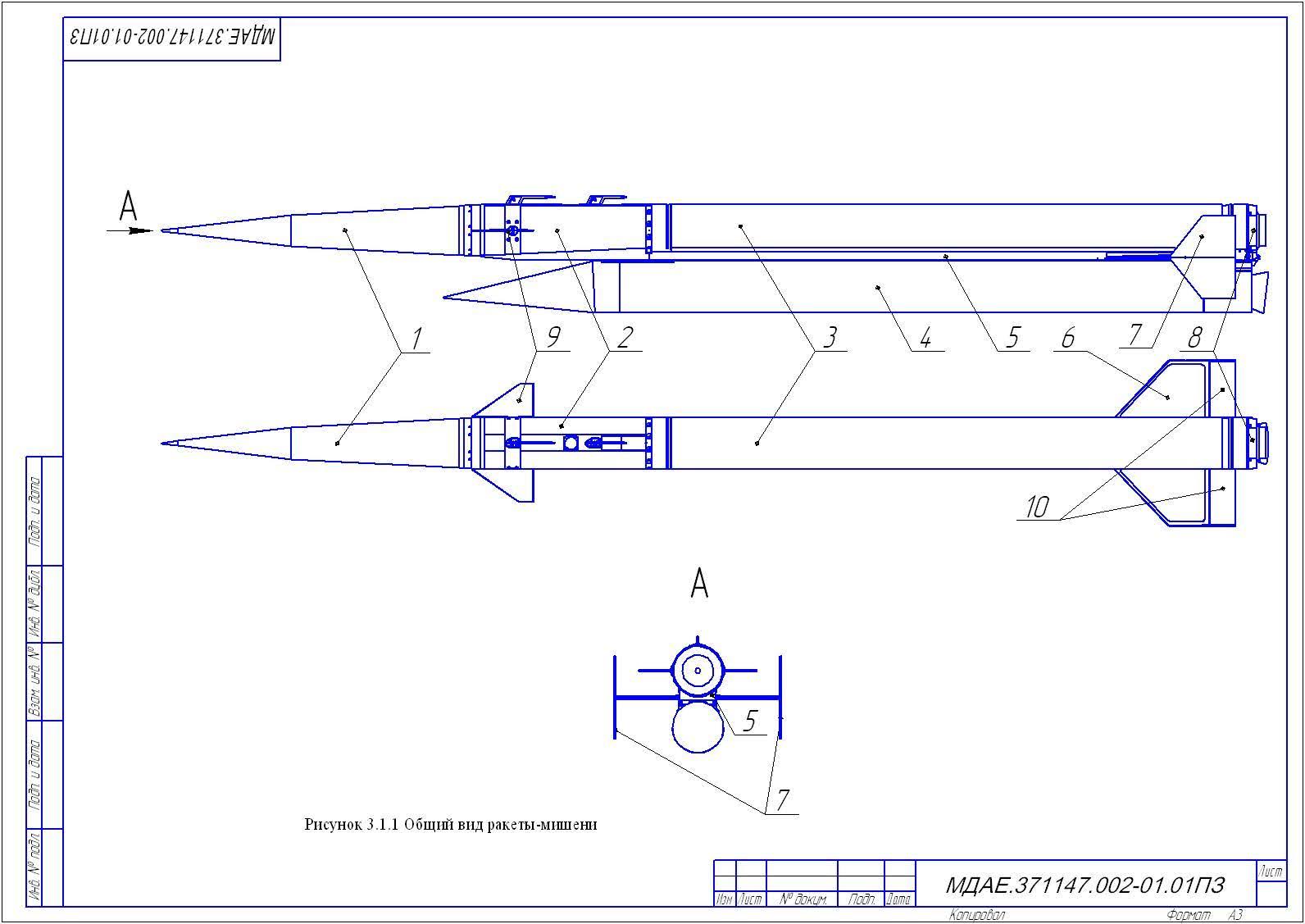
One of the “declassified” missiles turned out to be the new hypersonic “Carnation”. This is a target missile that is being developed for Russian air defense training in the fight against similar targets. The drawing and 3D model of the rocket, its characteristics, test results of specific components and information about the development participants were made public.
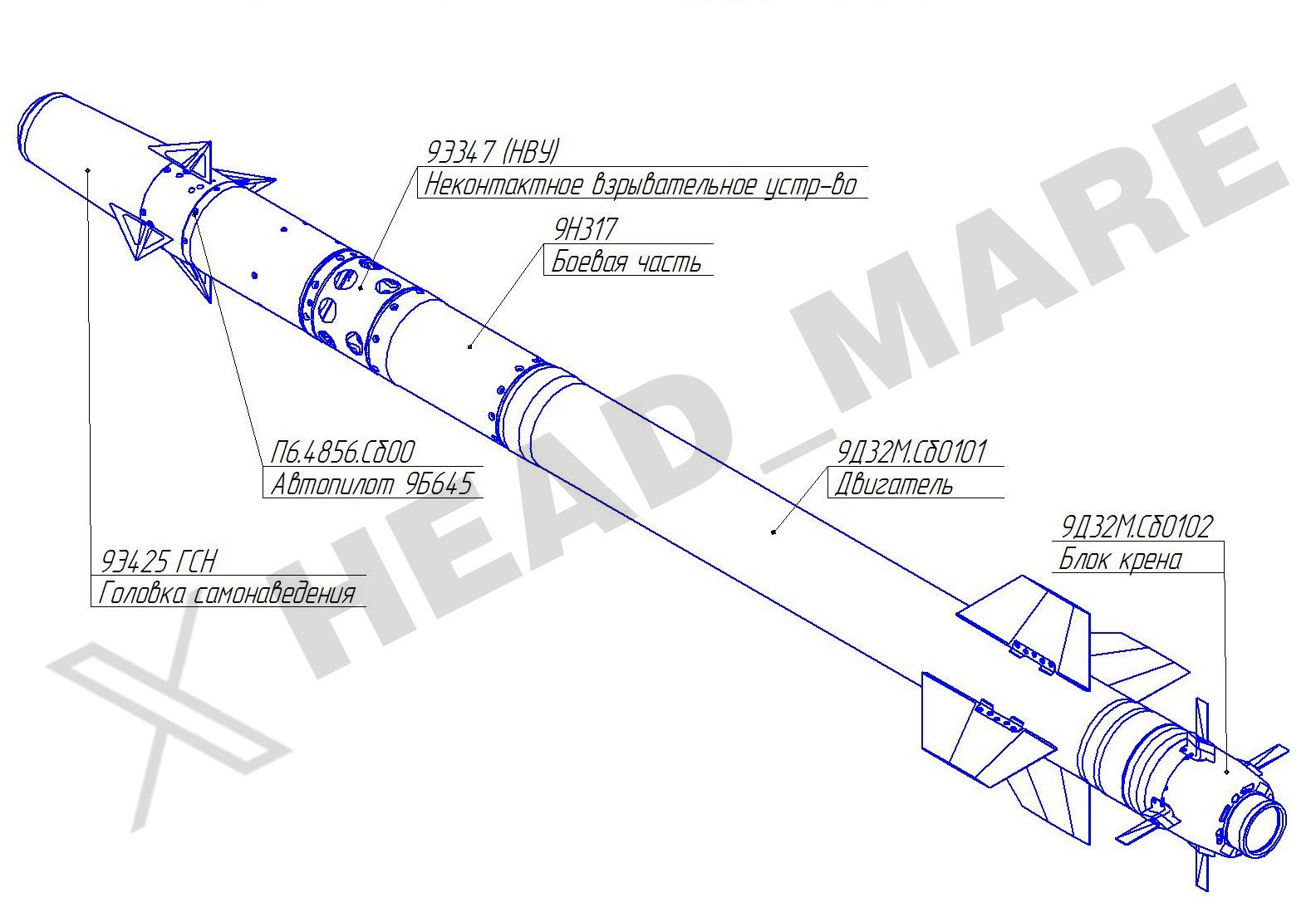
Hackers obtained data on the production and testing of a component of the 9M333 guided anti-aircraft missile. These missiles are used as ammunition for the Strela-10M4 9K35M4 air defense system, they have infrared homing.
 The development of the rocket was carried out for about 40 years, but it went into serial production only at the end of 2020.
The development of the rocket was carried out for about 40 years, but it went into serial production only at the end of 2020.
Hackers reported on the hack on X Twitter, where they specifically focused on the company’s poor cyber defenses and reporting on flaws in missile design. A complete set of documentation is available at the link.
The competition of ITS authors is ongoing. Write an article about game development, gaming and gaming devices and win a professional Logitech G923 Racing Wheel or one of the low-profile Logitech G815 LIGHTSYNC RGB Mechanical Gaming Keyboard!




