GitHub has enabled push protection for all public repositories by default. This is to prevent accidental disclosure of sensitive information such as access tokens and API keys when new code is shipped.
GitHub introduced this feature almost 2 years ago in April 2022. At that time, it was in beta status. It is positioned as a simple way to automatically prevent the leakage of confidential information. The feature became available to all public repositories in May 2023. It is currently activated as a standard feature, although it may take up to 2 weeks to become available.
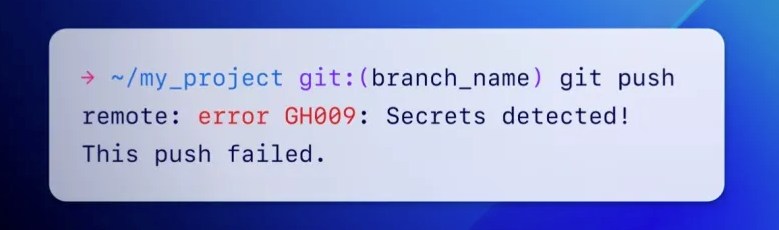
Push protection proactively prevents leaks by scanning for secrets before git pushes are committed. If confidential information is detected, commits are blocked.
This feature detects over 200 types of tokens and patterns from over 180 service providers (API keys, private keys, secret keys, authentication tokens, access tokens, management certificates, credentials, etc.).
If needed, users can disable push protection in security settings. Although it is not recommended to do this.
Source: bleepingcomputer
The competition of ITS authors is ongoing. Write an article about game development, gaming and gaming devices and win a professional Logitech G923 Racing Wheel or one of the low-profile Logitech G815 LIGHTSYNC RGB Mechanical Gaming Keyboard!




